In This Guide:
⏱️ Speed: Why vWAN cuts deployment time from weeks to minutes.
💰 Cost: A transparent breakdown of the £0.19/hr hub cost vs. operational savings.
🌍 Architecture: Moving from complex peering meshes to “Any-to-Any” global transit.
🗺️ Roadmap: A 4-phase strategy to migrate from Brownfield Hub-Spoke to vWAN without downtime.
The traditional approach to Azure networking through manually managed hub-and-spoke architectures served organisations well for single-region deployments, but enterprises expanding globally face mounting operational complexity. Managing multiple regional hubs, maintaining routing tables across dozens of virtual networks, and scaling VPN gateways whilst preserving transitive connectivity becomes increasingly unwieldy. Azure Virtual WAN addresses these enterprise-scale networking challenges through a fully managed service that transforms network architecture from an operational burden into a strategic capability.
Global enterprises managing multi-region Azure deployments recognise that network architecture directly impacts both operational efficiency and cloud TCO. Organisations operating 50+ branch offices across multiple continents, supporting thousands of remote users, or maintaining complex hybrid cloud environments require networking solutions that scale without linear increases in management overhead. Virtual WAN fundamentally changes the economics of enterprise Azure networking by replacing custom-built infrastructure with Microsoft-managed services, enabling network teams to focus on strategic initiatives rather than maintaining routing tables and troubleshooting VPN tunnels.
The market validates this shift. Enterprises adopting Virtual WAN report deployment times reducing from weeks to days, operational overhead decreasing by 40-60%, and simplified scaling that eliminates the need for regional gateway deployments. Financial services organisations managing global networks, retail chains connecting hundreds of locations, and healthcare providers maintaining compliance across regions demonstrate Virtual WAN’s capacity to address enterprise-scale requirements whilst reducing total cost of ownership.
The Evolution from Traditional Hub-Spoke to Virtual WAN
Azure’s traditional hub-and-spoke architecture established networking patterns that thousands of organisations deployed successfully. A central hub virtual network contains shared services – VPN gateways for on-premises connectivity, ExpressRoute circuits for private links, Azure Firewall or third-party network virtual appliances for security inspection, and shared infrastructure like domain controllers or monitoring systems. Spoke virtual networks peer with the hub, gaining transitive connectivity through user-defined routes that direct inter-spoke traffic through the hub’s routing infrastructure.
This model works effectively for organisations operating within single regions or managing limited numbers of spoke networks. Network teams gain centralised control over routing policies, security inspection points, and connectivity to on-premises environments. The architecture provides clear separation between workloads through isolated spoke networks whilst maintaining shared services in the hub that all spokes access.
Enterprise challenges emerge when organisations scale beyond regional boundaries or manage hundreds of spoke networks. Each additional Azure region requires deploying another hub-complete with VPN gateways, ExpressRoute connections, firewall infrastructure, and shared services. Connecting regional hubs requires additional virtual network peerings or VPN tunnels, creating complex routing dependencies. Network teams manually configure user-defined routes across expanding spoke networks, troubleshoot asymmetric routing issues, and manage gateway capacity as connectivity demands grow.
Operational overhead compounds with scale. Adding a new spoke network requires configuring virtual network peering, updating route tables in both the hub and other spokes for transitive connectivity, adjusting network security group rules, and validating routing paths. Deploying new regional hubs multiplies these tasks. Enterprises managing 100+ spoke networks across multiple regions often employ dedicated network operations teams solely to maintain routing configurations and troubleshoot connectivity issues.
Gateway capacity constraints create additional scaling challenges. VPN gateways in traditional hub-and-spoke architectures terminate all site-to-site VPN connections from branch offices. As organisations expand branch connectivity, they face gateway throughput limits-typically 1.25 Gbps per VPN tunnel-requiring complex configurations with multiple gateways and Border Gateway Protocol (BGP) load balancing. ExpressRoute gateways face similar scaling requirements as connectivity bandwidth grows.
Virtual WAN reimagines this architecture through managed services that eliminate manual configuration overhead. Rather than building hub infrastructure through virtual networks and manually deployed resources, organisations provision Virtual WAN hubs – Microsoft-managed constructs containing routing, VPN gateway, ExpressRoute gateway, and security infrastructure. Microsoft handles capacity scaling, high availability, routing automation, and infrastructure updates. Network teams define connectivity requirements and routing policies; Virtual WAN executes the implementation.
The architectural shift enables capabilities impossible in traditional hub-and-spoke deployments. Virtual WAN hubs automatically mesh, providing any-to-any connectivity between spokes across regional boundaries without manual peering or routing configuration. Branch offices connected to one regional hub can communicate with spokes in any region through Microsoft’s global backbone. Remote users connecting through point-to-site VPN gain access to resources across all connected virtual networks without complex routing configurations.
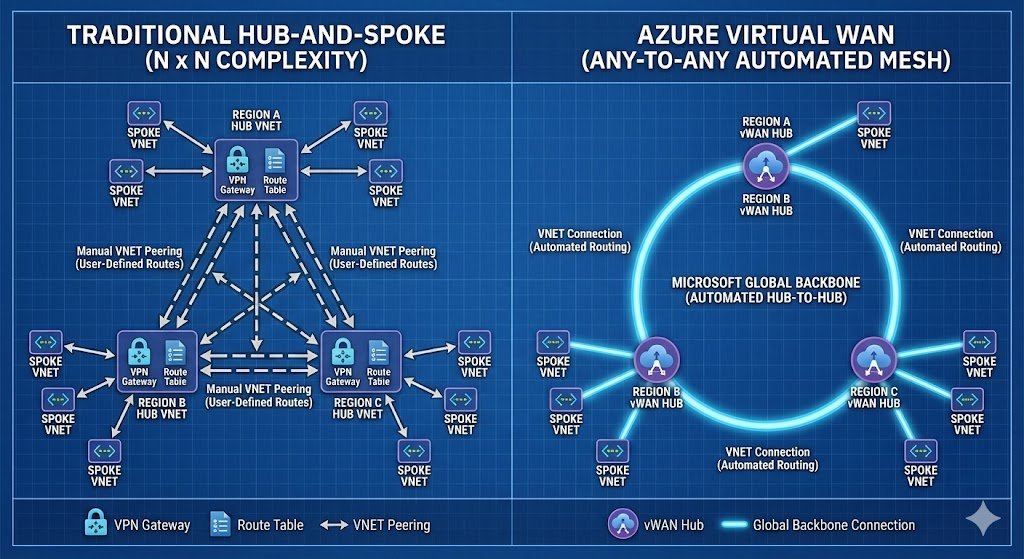
Transitive connectivity-the core challenge requiring elaborate user-defined routes in traditional hub-and-spoke-becomes automatic. Spoke virtual networks connected to a Virtual WAN hub can communicate directly through the hub’s routing infrastructure without manual route table configuration. This extends across hub-to-hub communications; spokes in different regions reach each other through the Microsoft global network without requiring virtual network peering between regional hubs.
Azure Virtual WAN Architecture Components
Virtual WAN architecture centres on the hub as a managed resource rather than a virtual network. Organisations create a Virtual WAN resource as a global construct, then deploy regional Virtual WAN hubs within that construct. Each hub represents a fully managed networking infrastructure in a specific Azure region, containing VPN gateways, ExpressRoute gateways, routing infrastructure, and optionally Azure Firewall for security inspection.
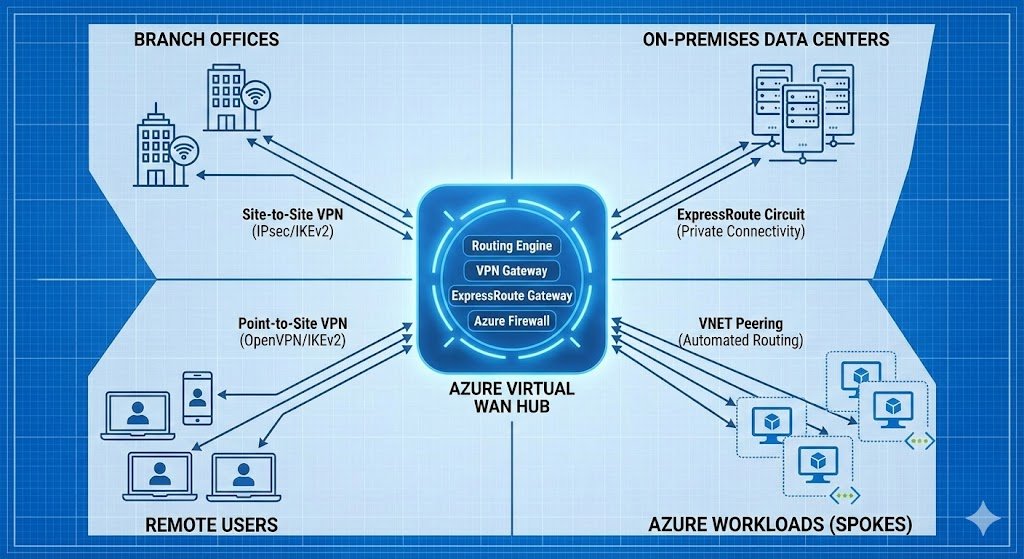
The hub’s routing engine provides the core functionality differentiating Virtual WAN from traditional architectures. This Microsoft-managed router automatically handles route propagation between connected endpoints-spoke virtual networks, VPN site connections, ExpressRoute circuits, and point-to-site user VPN connections. When a new spoke connects to the hub, the routing engine automatically propagates routes to all connected endpoints according to configured routing policies. This eliminates the manual user-defined route configuration required in traditional hub-and-spoke deployments.
Hub-to-hub connectivity operates through Microsoft’s global backbone network rather than requiring manual virtual network peering or VPN tunnels. When an organisation deploys Virtual WAN hubs in multiple regions – for example, UK South and North Europe – Microsoft automatically creates hub-to-hub connections. Traffic between spokes in different regions flows through these hub-to-hub links, leveraging Microsoft’s private backbone for inter-region transport. This provides global transit connectivity without organisations building and maintaining inter-region networking infrastructure.
Spoke virtual networks connect to Virtual WAN hubs through virtual network connections rather than traditional virtual network peering. These connections automatically configure routing between the spoke and all resources connected to the hub-other spokes, VPN sites, ExpressRoute circuits, and remote users. Network teams no longer configure user-defined routes in spoke subnets; the hub’s routing infrastructure handles path selection automatically based on configured routing policies.
VPN site connections represent branch offices or on-premises locations connecting through IPsec/IKEv2 VPN tunnels. Rather than terminating VPN connections on manually deployed VPN gateways, organisations define VPN sites in Virtual WAN that specify branch office network prefixes and public IP addresses. Virtual WAN’s managed VPN gateway establishes tunnels to these sites, scaling capacity automatically as connectivity demands grow. The service supports up to 20 Gbps aggregate VPN throughput per hub, far exceeding traditional VPN gateway limits.
ExpressRoute connections provide private connectivity from on-premises environments to Azure through dedicated circuits. Virtual WAN hubs include managed ExpressRoute gateways that terminate these circuits, with scaling from 2 Gbps up to 10 Gbps per scale unit. Organisations can deploy multiple ExpressRoute circuits to a single hub, with Virtual WAN handling route propagation and failover automatically.
Point-to-site user VPN connections enable remote users to access Azure resources through OpenVPN, IKEv2, or Azure VPN client connections. Virtual WAN hubs support up to 100,000 concurrent point-to-site connections per hub, addressing enterprise requirements for large-scale remote workforce connectivity. The service handles client IP allocation, authentication integration with Microsoft Entra ID, and automatic routing configuration for connected users.
Secured virtual hubs represent Virtual WAN hubs with integrated Azure Firewall and security policies managed through Azure Firewall Manager. This configuration provides centralised security inspection for traffic flowing through the hub – branch-to-Azure, inter-spoke, remote user traffic, and internet-bound connections. Rather than deploying and managing Azure Firewall instances manually in hub virtual networks, secured virtual hubs include fully managed firewall infrastructure that scales automatically.
Routing infrastructure within Virtual WAN hubs provides sophisticated traffic steering capabilities beyond basic transitive connectivity. Route tables within hubs enable network teams to implement network segmentation, directing specific spoke networks or VPN sites to isolated routing domains. This supports scenarios like separating production and development environments, implementing zero-trust network architecture, or routing traffic through network virtual appliances for inspection.
Traditional Hub-Spoke vs Virtual WAN: Decision Framework
Organisations evaluating network architecture approaches require clear decision criteria based on specific operational requirements rather than technology preferences. The architectural choice between traditional hub-and-spoke and Virtual WAN fundamentally depends on scale requirements, geographic distribution, operational team capabilities, and total cost of ownership considerations.
Traditional Hub-Spoke Architecture Advantages
Traditional hub-and-spoke architectures provide absolute control over network topology, routing decisions, and security implementation. Network teams design custom routing patterns, deploy preferred third-party network virtual appliances, and implement organisation-specific security policies without constraints imposed by managed services. This architectural flexibility proves valuable for organisations with unique compliance requirements, established relationships with specific security vendors, or networking teams expert in custom Azure networking configurations.
Resource placement within hub virtual networks remains entirely under organisation control. Network teams deploy specific virtual machine SKUs for network virtual appliances, configure custom monitoring solutions, and implement bespoke high availability patterns. This granular control enables organisations to optimise for specific performance requirements or integrate deeply with existing on-premises network management systems.
Cost predictability in traditional hub-and-spoke architectures stems from organisations paying only for resources they provision-virtual network peering, VPN gateways, ExpressRoute circuits, and network virtual appliance virtual machines. Organisations with relatively static networking requirements can precisely forecast costs based on deployed infrastructure without exposure to data processing charges that scale with traffic volume.
Established operational patterns represent another advantage for organisations already operating traditional hub-and-spoke architectures. Network teams understand troubleshooting methodologies, possess automation for deployment and configuration, and have established change management processes. Migrating to Virtual WAN requires operational transformation beyond technical architecture changes.
Traditional Hub-Spoke Architecture Limitations
Scale constraints emerge as the primary limitation driving organisations toward Virtual WAN. Each regional hub requires manual deployment of VPN gateways, ExpressRoute gateways, firewall infrastructure, and shared services. As organisations expand across regions, the operational burden of maintaining multiple regional hubs-each requiring configuration management, capacity planning, and troubleshooting-becomes substantial.
VPN gateway capacity limitations create scaling bottlenecks. Standard VPN gateways in traditional hub-and-spoke architectures provide 500 Mbps to 1.25 Gbps per tunnel, with maximum aggregate throughput of 10 Gbps through complex configurations involving multiple gateways and BGP routing. Organisations with hundreds of branch offices requiring higher bandwidth face expensive scaling challenges involving additional hub virtual networks and complex route distribution.
Routing complexity compounds with spoke network growth. Each new spoke requires configuring virtual network peering with the hub, creating user-defined routes for transitive connectivity to other spokes and on-premises networks, and updating network security groups. In deployments with 50+ spoke networks across multiple regions, routing table management becomes error-prone and time-consuming.
Hub-to-hub connectivity between regions requires manual configuration through virtual network peering or VPN tunnels. This adds latency compared to Microsoft backbone transport and creates additional configuration complexity. Organisations operating globally find themselves managing intricate mesh topologies between regional hubs or accepting sub-optimal routing that forces traffic through centralised hubs.
Operational overhead increases non-linearly with scale. Small deployments with single hubs and 10-20 spoke networks remain manageable. Enterprises operating 100+ spoke networks across 5-10 regions employ dedicated teams solely focused on network operations. This operational cost often exceeds the infrastructure cost savings from avoiding managed service charges.
Azure Virtual WAN Advantages
Automated routing configuration eliminates the manual user-defined route management required in traditional hub-and-spoke. When organisations connect spoke virtual networks, VPN sites, or ExpressRoute circuits to Virtual WAN hubs, routing propagation occurs automatically. New connectivity requires defining the connection; Virtual WAN handles route distribution across all connected endpoints. This automation reduces deployment time for new spoke networks from hours to minutes and eliminates common routing misconfiguration issues.
Hub-to-hub meshing through Microsoft’s global backbone provides any-to-any connectivity without manual configuration. Organisations deploy regional Virtual WAN hubs, and Microsoft automatically creates hub-to-hub connectivity. Spokes in different regions communicate through the Microsoft private backbone, reducing latency compared to routing through public internet or manually configured inter-region VPN tunnels.
Simplified scaling addresses the core challenge driving enterprise adoption. Virtual WAN hubs scale VPN and ExpressRoute gateway capacity automatically based on configured scale units, supporting up to 20 Gbps aggregate VPN throughput and 10+ Gbps ExpressRoute bandwidth per hub. Organisations add capacity by adjusting scale units rather than deploying additional gateway infrastructure and reconfiguring routing.
Global transit network capabilities enable sophisticated connectivity patterns impossible in traditional architectures. Branch offices can communicate directly with each other through Virtual WAN hubs without traffic routing through on-premises data centres. Remote users connecting through point-to-site VPN gain access to all connected networks-spokes, on-premises via ExpressRoute, and other branches-without complex routing configurations.
Operational simplification represents Virtual WAN’s most significant advantage for large-scale deployments. Network teams define connectivity requirements and routing policies; Microsoft manages infrastructure capacity, high availability, routing propagation, and service updates. This reduces the operational team size required to manage global networking infrastructure, enabling network engineers to focus on strategic initiatives rather than troubleshooting routing issues.
Integrated security through secured virtual hubs combines networking and security infrastructure in a single managed service. Rather than deploying and scaling Azure Firewall separately, secured virtual hubs include fully managed firewall capacity that scales with traffic demands. Azure Firewall Manager provides centralised policy management across all secured hubs, simplifying security operations for multi-region deployments.
Azure Virtual WAN Limitations
Cost structure differences require careful analysis. Virtual WAN charges for hub deployment hours (£0.19/hour per hub), connection units (£0.0036/hour per VPN or VNet connection), scale units (£0.27/hour per VPN scale unit, £0.31/hour per ExpressRoute scale unit), and data processing (£0.018/GB for VNet-to-VNet traffic through the hub router). For organisations with relatively static, low-traffic deployments, these charges may exceed traditional hub-and-spoke infrastructure costs.
Network virtual appliance deployment in Virtual WAN hubs supports limited third-party solutions compared to the flexibility of deploying any NVA in traditional hub virtual networks. Whilst major vendors like Palo Alto Networks, Fortinet, and Check Point provide Virtual WAN hub integrations, organisations with specific NVA requirements may face deployment constraints or require hybrid architectures combining Virtual WAN with traditional hub-and-spoke elements.
Routing policy flexibility, whilst sophisticated through route tables and routing intent configurations, doesn’t match the absolute control available through custom user-defined routes in traditional architectures. Organisations requiring highly specific routing behaviours may find Virtual WAN’s routing engine lacks certain edge-case capabilities available through manual configuration.
Migration complexity from existing traditional hub-and-spoke deployments represents a significant consideration. Organisations can’t simply convert hub virtual networks to Virtual WAN hubs; migration requires parallel deployment of Virtual WAN infrastructure, gradual spoke network migration, and eventual decommissioning of traditional hubs. This process demands careful planning to maintain connectivity during transition and may require temporary hybrid architectures.
Decision Criteria
Organisations should deploy traditional hub-and-spoke architectures when operating within single Azure regions with fewer than 30 spoke networks, requiring absolute control over network virtual appliance selection and routing configuration, managing static networking requirements with predictable traffic patterns, or possessing expert networking teams capable of managing custom routing configurations.
Virtual WAN provides compelling advantages for organisations managing multiple Azure regions requiring hub-to-hub connectivity, deploying 50+ spoke networks with frequent additions, connecting 20+ branch offices through site-to-site VPN, supporting 1,000+ remote users through point-to-site VPN, requiring global transit network capabilities, or seeking to reduce networking operational team size.
Hybrid architectures combining both approaches suit organisations mid-migration from traditional hub-and-spoke to Virtual WAN, requiring specific network virtual appliance capabilities available only in virtual network deployments alongside Virtual WAN’s global connectivity benefits, or managing compliance requirements that mandate certain workloads remain in traditional hub-and-spoke whilst others leverage Virtual WAN.
Real-World Enterprise Implementations
Financial services organisations demonstrate Virtual WAN’s capability to address complex global networking requirements. A multinational bank operating across European, Asian, and North American markets deployed Virtual WAN hubs in six regions, connecting 200+ branch offices through site-to-site VPN and 120+ spoke virtual networks containing production and development workloads. The bank replaced their traditional hub-and-spoke architecture that required dedicated network operations teams in each region with centralised Virtual WAN management, reducing operational overhead by 45% whilst improving deployment times for new branch offices from weeks to hours.
The bank’s implementation leverages secured virtual hubs with Azure Firewall Manager for centralised security policy enforcement across all regions. All branch-to-Azure traffic, inter-spoke communications, and internet-bound connections flow through Azure Firewall, meeting regulatory requirements for traffic inspection and logging. The bank reports 90% reduction in security policy configuration time across their global network compared to managing separate Azure Firewall instances in traditional hub virtual networks.
Retail organisations with extensive branch networks showcase Virtual WAN’s site-to-site VPN scaling capabilities. A European retail chain operating 500+ stores across 15 countries migrated from MPLS-based wide area networking to Azure Virtual WAN with branch offices connecting through SD-WAN devices. Each store connects to the nearest regional Virtual WAN hub through IPsec VPN tunnels, gaining access to centralised applications hosted in Azure spoke virtual networks and on-premises data centre resources via ExpressRoute.
The retail implementation demonstrates cost optimisation through replacing expensive MPLS circuits with internet-based VPN connectivity. The organisation reports 60% reduction in wide area network costs whilst improving bandwidth capacity at branch locations from 10 Mbps MPLS to 100+ Mbps internet connections. Virtual WAN’s automatic routing enabled the retail chain to implement disaster recovery patterns where stores failing over to alternate data centres maintain connectivity without manual routing reconfiguration.
Healthcare providers managing compliance requirements across distributed locations illustrate Virtual WAN’s secured virtual hub capabilities. A healthcare organisation operating hospitals, clinics, and administrative offices across multiple regions deployed Virtual WAN with secured virtual hubs to centralise security inspection whilst maintaining network segmentation between patient care networks, administrative systems, and research environments. The implementation leverages Virtual WAN route tables to isolate routing domains, ensuring patient care networks cannot communicate directly with research networks whilst both access shared services.
The healthcare deployment integrated point-to-site user VPN supporting 5,000+ remote clinical staff accessing electronic health record systems hosted in Azure. Virtual WAN’s point-to-site VPN scaling to 100,000 concurrent connections per hub eliminated the gateway capacity constraints the organisation faced with traditional VPN gateways. The implementation reduced support incidents related to remote access connectivity by 70% through simplified user VPN client configuration and automatic routing to all required resources.
Manufacturing organisations with globally distributed operations leverage Virtual WAN’s hub-to-hub mesh connectivity for inter-region communications. A manufacturing enterprise operating production facilities across Asia, Europe, and North America deployed Virtual WAN hubs in five regions with spoke virtual networks hosting manufacturing execution systems, enterprise resource planning applications, and industrial IoT data platforms. The hub-to-hub mesh enables production facilities in different regions to share manufacturing data, synchronise inventory systems, and access centralised analytics platforms without traffic routing through headquarters.
The manufacturing implementation demonstrates Virtual WAN’s support for hybrid connectivity patterns. Production facilities connect through ExpressRoute circuits for high-bandwidth, low-latency connectivity to Azure resources, whilst smaller administrative offices connect through site-to-site VPN. Virtual WAN’s automated routing enables seamless communications between ExpressRoute-connected facilities and VPN-connected offices without manual route redistribution configuration.
Cost Analysis and Total Cost of Ownership
Virtual WAN pricing comprises four primary components that organisations must evaluate against traditional hub-and-spoke infrastructure costs. Hub deployment charges £0.19 per hour per hub (approximately £140 monthly per hub), covering the managed infrastructure containing routing, VPN gateway, and ExpressRoute gateway components. Organisations deploying hubs in three regions incur £420 monthly base hub costs before connection or scale unit charges.
Connection unit pricing charges £0.0036 per hour per connection for VPN site connections and virtual network connections to hubs. An organisation connecting 50 spoke virtual networks and 30 VPN sites pays approximately £260 monthly for connection units. This represents ongoing costs that scale linearly with spoke networks and branch offices, contrasting with traditional hub-and-spoke architectures where virtual network peering costs vary by data transfer volume rather than connection count.
Scale units determine VPN and ExpressRoute gateway capacity. VPN scale units (500 Mbps aggregate capacity per unit) cost £0.27 per hour (£200 monthly), with organisations deploying up to 40 scale units (20 Gbps aggregate capacity) per hub. ExpressRoute scale units (2 Gbps capacity for units 1-5, scaling costs for units 6-10) cost £0.31 per hour (£230 monthly) for baseline capacity. Organisations requiring 10 Gbps ExpressRoute bandwidth deploy five scale units at £1,150 monthly.
Data processing charges for traffic flowing through the Virtual WAN hub router cost £0.018 per GB for VNet-to-VNet connections. Organisations moving substantial traffic between spoke virtual networks incur data processing costs alongside standard Azure data egress charges. A deployment transferring 10 TB monthly between spokes pays £180 monthly for hub data processing plus regional data transfer charges.
Traditional hub-and-spoke infrastructure costs differ substantially in structure. VPN gateways range from £130 monthly for Basic SKU (100 Mbps) to £3,900 monthly for VpnGw5 SKU (10 Gbps). Organisations requiring 20 Gbps aggregate VPN capacity matching Virtual WAN’s maximum require deploying multiple VPN gateways with BGP load balancing, incurring £7,800+ monthly for gateway infrastructure alone plus operational costs for managing complex routing.
ExpressRoute gateways cost £260 monthly for Standard SKU (2 Gbps) up to £12,700 monthly for ErGw3AZ SKU (10 Gbps). Virtual network peering between hub and spoke networks costs £0.0036 per GB in UK regions for inbound traffic and £0.0036 per GB for outbound traffic, meaning organisations transferring substantial traffic between hub and spokes incur ongoing data transfer charges similar to Virtual WAN data processing fees.
Azure Firewall deployed in traditional hub virtual networks costs from £740 monthly for Standard SKU up to £5,500 monthly for Premium SKU with 100 Gbps capacity. Virtual WAN secured virtual hubs include Azure Firewall at the same pricing, but organisations benefit from centralised management through Azure Firewall Manager without additional operational overhead.
TCO analysis requires evaluating infrastructure costs alongside operational expenses. Traditional hub-and-spoke deployments with multiple regional hubs require network engineering staff to manage routing configurations, troubleshoot connectivity issues, scale gateway capacity, and deploy new spoke networks. Enterprises commonly employ 2-3 network engineers focused solely on Azure networking operations for large-scale traditional hub-and-spoke deployments, representing £150,000-£250,000 annual salary costs. Effective FinOps practices evaluate these total costs rather than infrastructure expenses alone.
Virtual WAN reduces operational team requirements through automation, with organisations reporting 40-60% reduction in networking operational effort. This operational efficiency translates to either reduced staffing requirements or reallocation of network engineering capacity to strategic initiatives like implementing zero-trust architecture or optimising application performance. Over three-year periods, operational cost savings often exceed any infrastructure cost differences.
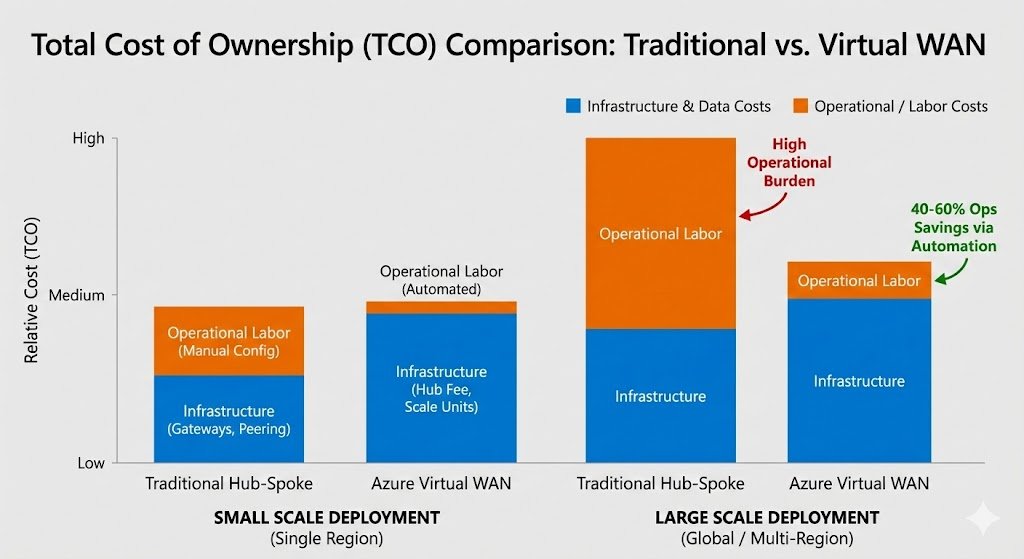
Small-scale deployments favour traditional hub-and-spoke from pure infrastructure cost perspectives. An organisation operating single-region with 10 spoke networks and one VPN gateway pays approximately £130 monthly for gateway plus virtual network peering data transfer charges, compared to £350+ monthly for equivalent Virtual WAN deployment (hub fee, connection units, and scale unit). Operational simplicity advantages don’t offset higher infrastructure costs at this scale.
Medium-scale deployments with multi-region requirements show Virtual WAN achieving cost parity. An organisation deploying three regional hubs with 50 spoke networks total and substantial inter-region traffic pays similar infrastructure costs for either architecture but gains significant operational efficiency advantages with Virtual WAN. The automation reducing deployment times and eliminating routing configuration overhead justifies infrastructure costs.
Large-scale global deployments demonstrate clear Virtual WAN TCO advantages. Organisations managing 100+ spoke networks across five regions, connecting 50+ branch offices, and supporting 2,000+ remote users find Virtual WAN’s infrastructure costs comparable to traditional hub-and-spoke whilst operational costs reduce by 40-60%. Three-year TCO analysis shows 25-40% overall cost reduction when accounting for both infrastructure and operational expenses.
Implementation Roadmap and Migration Strategy
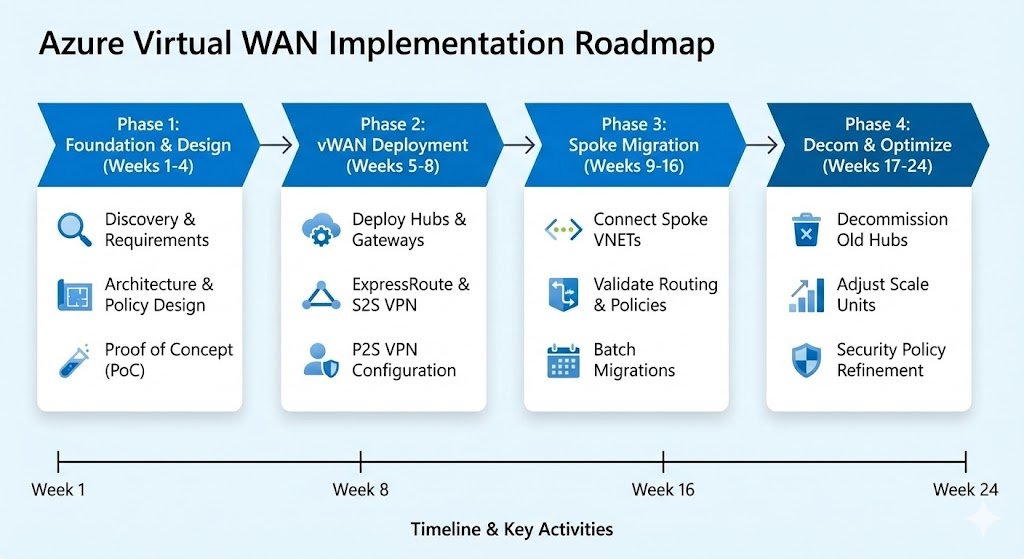
Organisations deploying Virtual WAN benefit from phased implementation approaches that validate architecture decisions whilst minimising risk. Greenfield deployments launching new Azure environments can deploy Virtual WAN directly, whilst brownfield migrations from existing traditional hub-and-spoke require careful planning to maintain connectivity during transition.
Phase 1: Foundation and Design (Weeks 1-4)
Initial planning establishes connectivity requirements, routing policies, and security architecture. Network teams document existing branch office locations, required bandwidth for site-to-site VPN connections, ExpressRoute circuit requirements for on-premises data centres, point-to-site user VPN capacity for remote workers, and spoke virtual network segmentation requirements. This documentation informs scale unit sizing, hub regional placement, and routing table design.
Organisations map current traditional hub-and-spoke architectures to equivalent Virtual WAN designs, identifying workloads suitable for initial migration, network virtual appliances requiring replacement or integration, routing policies requiring Virtual WAN route table implementation, and security policies migrating to Azure Firewall Manager. This mapping enables accurate cost comparison between maintaining traditional architecture versus Virtual WAN migration.
Security policy design for secured virtual hubs translates existing Azure Firewall rules and network security group configurations into Azure Firewall Manager policies. Network teams establish routing intent configurations for traffic inspection requirements, route table designs for network segmentation, and integration patterns for third-party security information and event management systems.
Proof of concept deployments in isolated environments validate design decisions before production implementation. Organisations deploy Virtual WAN in separate Azure subscriptions, connect test spoke networks, implement security policies, and validate routing behaviour. This proof of concept identifies configuration requirements and potential issues before affecting production environments.
Phase 2: Virtual WAN Deployment (Weeks 5-8)
Production Virtual WAN deployment begins with provisioning the global Virtual WAN resource and regional hubs. Organisations create Virtual WAN hubs in each required Azure region, configuring scale units based on bandwidth requirements, enabling secured virtual hub for regions requiring centralized security inspection, and deploying managed VPN gateways for site-to-site connectivity.
ExpressRoute circuit integration connects on-premises data centres to Virtual WAN hubs through existing circuits. Organisations create ExpressRoute connections in Virtual WAN hubs, validate route propagation from on-premises to hub, and test connectivity between on-premises and test spoke networks. This establishes hybrid connectivity foundation before migrating production spoke networks.
Site-to-site VPN configuration connects branch offices to Virtual WAN. Network teams define VPN sites specifying branch office network prefixes and public IP addresses, establish IPsec tunnels between branch VPN devices and Virtual WAN hubs, and validate branch connectivity to Azure resources. SD-WAN integrations through Virtual WAN partner devices automate configuration for organisations deploying SD-WAN solutions.
Point-to-site user VPN deployment enables remote worker connectivity. Organisations configure authentication integration with Microsoft Entra ID, deploy VPN client configuration profiles to end-user devices, and test remote access to Azure resources. Virtual WAN’s support for 100,000 concurrent connections per hub addresses enterprise-scale remote workforce requirements.
Phase 3: Spoke Network Migration (Weeks 9-16)
Gradual spoke network migration maintains connectivity during transition from traditional hub-and-spoke to Virtual WAN. Organisations identify low-risk spoke networks for initial migration-typically development or non-production environments-and establish migration procedures applicable to production spokes.
Each spoke migration involves creating virtual network connection to Virtual WAN hub, validating automatic routing propagation to branch offices and on-premises networks, testing application connectivity through the hub, and removing traditional hub virtual network peering. Organisations migrate spokes in batches of 5-10, validating connectivity before proceeding to subsequent batches.
Production spoke networks require careful scheduling to minimise application downtime. Network teams coordinate with application owners for migration windows, implement monitoring to detect connectivity issues quickly, and maintain rollback procedures to restore traditional hub-and-spoke connectivity if problems occur. Most organisations report spoke migration windows of 15-30 minutes per spoke for actual connectivity changes.
Routing policy implementation through Virtual WAN route tables establishes network segmentation equivalent to traditional hub-and-spoke user-defined routes. Organisations create route tables for production versus development environment isolation, implement routing intent for security inspection through Azure Firewall, and configure custom routes for traffic steering through network virtual appliances when required.
Phase 4: Decommissioning and Optimisation (Weeks 17-24)
Traditional hub infrastructure decommissioning occurs after validating all spoke networks migrated successfully. Organisations monitor for several weeks post-migration, confirming no connectivity issues or routing problems, before removing traditional hub virtual networks. This conservative approach maintains fallback options during validation period.
Cost optimisation reviews Virtual WAN scale unit sizing, connection unit requirements, and data processing patterns. Organisations analyse actual traffic flows, adjust VPN scale units to match observed bandwidth requirements, optimise ExpressRoute scale units based on utilisation, and review spoke connection requirements to eliminate unused connections.
Security policy refinement translates lessons learned from initial secured virtual hub deployment into optimised Azure Firewall Manager policies. Network teams review firewall logs to identify traffic patterns, adjust security rules to eliminate false positives whilst maintaining protection, and implement threat intelligence integration for enhanced security.
Operational procedures establish ongoing Virtual WAN management practices. Organisations document procedures for adding new spoke networks, connecting new branch offices, implementing routing policy changes, and monitoring hub performance. This operational foundation enables network teams to leverage Virtual WAN’s automation whilst maintaining governance over network architecture.
Future Trends and Strategic Considerations
Virtual WAN’s roadmap emphasises deeper integration with Microsoft’s broader networking and security portfolio. Enhanced Azure Firewall capabilities within secured virtual hubs include TLS inspection for encrypted traffic analysis, intrusion detection and prevention system features, and improved threat intelligence integration. These security enhancements position Virtual WAN secured virtual hubs as comprehensive security services edge rather than routing infrastructure with basic firewall capabilities.
Network virtual appliance integration continues expanding through Virtual WAN partner ecosystem growth. Major security vendors increasingly provide managed appliance offerings specifically designed for Virtual WAN hub deployment, combining network security, SD-WAN optimisation, and application acceleration in integrated solutions. This trend addresses enterprises requiring advanced security capabilities beyond Azure Firewall whilst maintaining Virtual WAN’s operational simplicity.
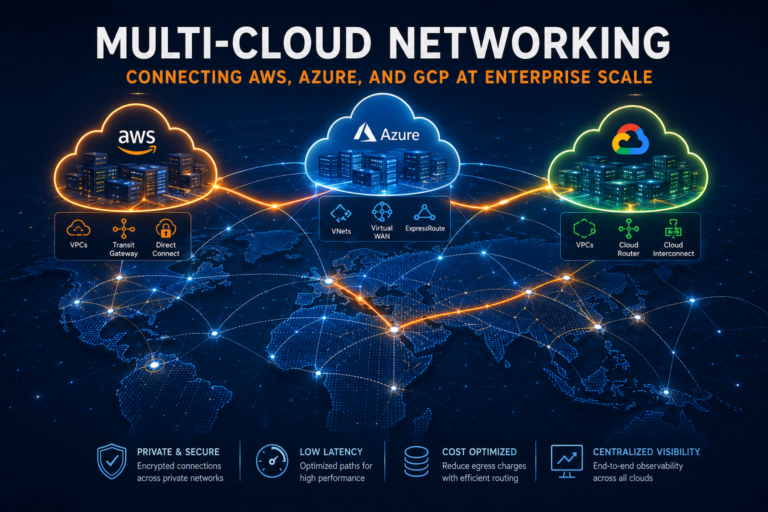
Multi-cloud networking integration represents longer-term strategic evolution. Whilst Virtual WAN currently focuses on Azure connectivity and hybrid scenarios, Microsoft’s broader networking vision includes simplified multi-cloud connectivity through Azure. Organisations deploying workloads across Azure, AWS, and Google Cloud Platform may eventually leverage Virtual WAN as global transit hub connecting multiple cloud providers, though this capability remains on strategic roadmaps rather than current product offerings.
Private 5G network integration positions Virtual WAN as connectivity foundation for industrial IoT and edge computing scenarios. Enterprises deploying private 5G networks for manufacturing, logistics, or campus connectivity increasingly require Azure integration for IoT data platforms, AI analytics, and application hosting. Virtual WAN’s hub-and-spoke architecture with branch office connectivity through site-to-site VPN provides natural integration point for private 5G core networks.
Zero-trust network architecture implementation benefits from Virtual WAN’s routing and security capabilities. Organisations implementing zero-trust principles require network segmentation, traffic inspection, and identity-based access controls across distributed environments. Virtual WAN’s route tables enable micro-segmentation, secured virtual hubs provide comprehensive traffic inspection, and integration with Microsoft Entra ID supports identity-based routing policies.
Sustainability considerations influence networking architecture decisions as organisations measure and reduce cloud carbon footprints. Virtual WAN’s efficiency advantages-optimised routing through Microsoft backbone, automated scaling reducing over-provisioned capacity, and elimination of redundant infrastructure through managed services-contribute to reduced energy consumption compared to traditional hub-and-spoke architectures requiring organisations to provision peak capacity.
Recommended Architecture Patterns
Organisations deploying Virtual WAN should establish hub placement strategies based on regional presence, regulatory requirements, and performance objectives. Multi-region enterprises benefit from deploying hubs in each Azure region containing spoke networks, typically resulting in 3-5 regional hubs for global organisations. This regional hub placement minimises latency between spokes and hubs whilst leveraging hub-to-hub mesh for inter-region connectivity.
Branch office connectivity architecture depends on office size and bandwidth requirements. Large branch offices with 100+ users benefit from ExpressRoute circuits providing dedicated private connectivity, measured latency, and higher bandwidth. Smaller branch offices with 10-50 users cost-effectively connect through site-to-site VPN with SD-WAN devices optimising application performance over internet connectivity. This hybrid approach balances connectivity costs with performance requirements.
Secured virtual hub deployment strategy requires evaluating traffic inspection requirements against cost implications. Organisations with regulatory mandates for comprehensive traffic inspection deploy secured virtual hubs with Azure Firewall in all regions, accepting the £740+ monthly firewall cost per region. Organisations with less stringent requirements deploy secured virtual hubs only in regions containing sensitive workloads, routing other region traffic through those hubs for inspection when necessary.
Route table design implements network segmentation equivalent to traditional hub-and-spoke user-defined routes whilst leveraging Virtual WAN’s automation. Organisations create route tables for production environment isolation, development and test environment separation, shared services access, and DMZ networks requiring internet exposure. Spoke virtual network associations with specific route tables enforce segmentation policies without requiring user-defined routes in spoke subnets.
Disaster recovery patterns leverage Virtual WAN’s multi-region architecture for automated failover. Organisations deploy application resources in primary and secondary regions with spokes in both regions connected to respective Virtual WAN hubs. Hub-to-hub mesh enables applications failing over to secondary regions to maintain connectivity to on-premises resources via either region’s ExpressRoute connection, eliminating single points of failure in hybrid connectivity. Understanding Azure’s resilience building blocks helps organisations design effective multi-region disaster recovery strategies.
Strategic Recommendations
Organisations managing single-region Azure deployments with fewer than 30 spoke networks and limited growth expectations benefit from traditional hub-and-spoke architectures. The infrastructure cost advantages, absolute control over routing configuration, and lower operational complexity for small-scale deployments outweigh Virtual WAN’s automation benefits. These organisations should monitor growth; migration to Virtual WAN becomes compelling when expanding beyond single regions or exceeding 50 spoke networks. Business leaders evaluating cloud strategy should understand how network architecture decisions impact both immediate costs and long-term operational efficiency.
Multi-region enterprises operating three or more Azure regions with 50+ spoke networks across regions should deploy Virtual WAN. The hub-to-hub mesh connectivity, automated routing propagation, and operational efficiency advantages justify infrastructure costs at this scale. Implementation should proceed through phased approach starting with single region proof of concept, expanding to additional regions after validating architecture decisions.
Organisations mid-migration from on-premises to Azure benefit from deploying Virtual WAN immediately rather than implementing traditional hub-and-spoke as intermediate architecture. Virtual WAN’s ExpressRoute integration, site-to-site VPN for branch offices, and point-to-site VPN for remote users provide comprehensive hybrid connectivity foundation. This approach avoids double migration-first implementing traditional hub-and-spoke then subsequently migrating to Virtual WAN as scale demands.
Greenfield Azure deployments should evaluate Virtual WAN as default networking architecture unless specific requirements mandate traditional hub-and-spoke control. The automation reducing initial deployment time, built-in high availability, and simplified scaling enable organisations to focus on application deployment rather than network infrastructure configuration. Even small-scale deployments benefit from operational simplicity, though infrastructure costs may exceed traditional approaches.
Security-focused organisations requiring comprehensive traffic inspection across all Azure connectivity should implement secured virtual hubs with Azure Firewall Manager. The centralised policy management, simplified deployment across multiple regions, and automated scaling address enterprise security operations requirements. Organisations with existing third-party security appliance investments can deploy those appliances in spoke virtual networks with routing intent policies directing traffic through security spokes before reaching applications.
Virtual WAN represents fundamental shift in enterprise Azure networking from manually configured infrastructure to automation-driven managed services. The architecture addresses operational challenges organisations face at scale whilst enabling global transit network capabilities impossible in traditional hub-and-spoke deployments. Enterprises expanding Azure presence globally find Virtual WAN’s combination of simplified operations, comprehensive connectivity patterns, and integrated security capabilities justify the architectural transformation from custom networking infrastructure to Microsoft-managed services.
Useful Links
- Azure Virtual WAN Documentation – Comprehensive official documentation covering features, architecture, and configuration
- Virtual WAN Pricing – Current pricing for hubs, scale units, and connection units
- Hub-Spoke with Virtual WAN Architecture – Microsoft architecture guidance for implementing hub-spoke using Virtual WAN
- Migrate to Azure Virtual WAN – Migration guidance from traditional hub-and-spoke to Virtual WAN
- Virtual WAN Partners and Locations – SD-WAN and VPN partner devices supporting Virtual WAN integration
- Azure Firewall Manager – Documentation for managing security policies across Virtual WAN secured virtual hubs
- Virtual WAN FAQ – Frequently asked questions covering common implementation scenarios
- Virtual WAN Route Tables – Routing configuration guidance for network segmentation
- ExpressRoute and Virtual WAN – Integration patterns for ExpressRoute connectivity
- Point-to-Site VPN for Virtual WAN – Configuration guidance for remote user VPN connectivity