Azure networking architecture decisions directly impact operational costs, security posture, and organisational agility for the next 3-5 years. Enterprises managing multi-region, multi-subscription Azure environments face a critical choice between three distinct networking models: traditional Hub-Spoke, Azure Virtual WAN, and the emerging Azure Virtual Network Manager. These decisions carry significant financial implications, with organisations operating 50+ virtual networks potentially facing cost differentials of £40,000-£120,000 annually between approaches.
The global software-defined wide area network market, which includes Azure networking solutions, reached $4.8 billion in 2024 and is projected to grow at 24.3% CAGR through 2030. Microsoft reports that 78% of Azure enterprise customers now operate hub-spoke topologies, whilst Virtual WAN adoption has increased 145% year-over-year amongst organisations managing multi-region deployments. The introduction of Azure Virtual Network Manager in general availability represents Microsoft’s strategic response to enterprises seeking centralised network management without the cost overhead of full Virtual WAN implementations.
This comprehensive analysis examines all three Azure networking architectures through the lens of enterprise decision-making, providing specific cost breakdowns, security comparisons, performance characteristics, and clear migration pathways for organisations transitioning from on-premises networks or evolving their existing Azure infrastructure.
Current State of Azure Networking
Azure networking architecture has evolved considerably since the platform’s inception, moving from simple flat network designs to sophisticated hub-spoke topologies and now cloud-native SD-WAN implementations. Traditional hub-spoke architectures emerged around 2015-2016 as enterprises sought to centralise security controls whilst maintaining network segmentation. This pattern, borrowed from on-premises data centre design, became the de facto standard for Azure enterprise deployments, particularly for organisations managing hybrid cloud environments across Azure and on-premises infrastructure.
Azure Virtual WAN launched in 2018 as Microsoft’s answer to the complexity challenges facing organisations managing global Azure footprints. Rather than manually configuring VNet peering and route tables across dozens of locations, Virtual WAN provides an abstraction layer that automates much of the network topology management. The service targets enterprises with significant multi-region requirements, branch office connectivity needs, or complex SD-WAN integrations.
Azure Virtual Network Manager, reaching general availability in 2023, represents Microsoft’s latest evolution in network management tooling. AVNM addresses a gap between manual hub-spoke management and full Virtual WAN deployments, offering centralised policy management, security admin rules, and connectivity management at a fraction of Virtual WAN’s cost. Early adopters report 60-70% reduction in network configuration time compared to manual hub-spoke management, whilst avoiding the 300-500% cost premium associated with Virtual WAN for purely intra-Azure connectivity scenarios.
The conversation in enterprise architecture teams has shifted from “should we use hub-spoke?” to “which networking model optimises our specific requirements around cost, security, performance, and operational complexity?” Financial services organisations prioritise security isolation and regulatory compliance. Manufacturing firms emphasise low-latency connectivity between IoT endpoints and analytics platforms. Global retailers require seamless integration between Azure regions and existing SD-WAN infrastructure for thousands of branch locations.
A common misconception persists that Virtual WAN represents the natural evolution path for all hub-spoke deployments. Whilst Virtual WAN excels for specific use cases, particularly those involving branch connectivity or global transit architectures, it introduces unnecessary complexity and cost for organisations primarily concerned with intra-Azure connectivity. Similarly, Azure Virtual Network Manager shouldn’t be viewed as a simplified version of Virtual WAN, it’s an entirely different architectural approach optimised for centralised management of traditional hub-spoke or mesh topologies.
Technical Architecture Deep-Dive
Hub-Spoke Topology: Traditional Centralised Architecture
Hub-spoke architecture establishes a central hub virtual network containing shared services (firewalls, VPN gateways, ExpressRoute connections) with multiple spoke VNets peered to the hub. Traffic between spokes must transit through the hub, creating a centralised point for security policy enforcement, logging, and connectivity to on-premises networks.

Core Components:
The hub VNet typically deploys in a dedicated subscription with three primary subnets: GatewaySubnet for VPN/ExpressRoute gateways, AzureFirewallSubnet or network virtual appliance (NVA) subnet for traffic inspection, and a management subnet for administrative services. Organisations commonly size hub VNets with /22 or /23 address space to accommodate growth in shared services.
Spoke VNets deploy in application-specific or environment-specific subscriptions (development, production, specific business units). Each spoke peers to the hub using Azure VNet Peering with “Use Remote Gateway” enabled, allowing spoke resources to leverage the hub’s VPN or ExpressRoute connectivity. User Defined Routes (UDRs) on spoke subnets force traffic destined for other spokes or on-premises through the hub firewall or NVA.
Traffic Flow Patterns:
Spoke-to-spoke traffic follows this path: Source spoke → Hub firewall/NVA → Destination spoke. This introduces approximately 2-3ms additional latency compared to direct peering, but enables centralised security policy enforcement. Spoke-to-internet traffic can either route through the hub firewall (force-tunnelling) or egress directly via Azure’s default route, depending on security requirements.
On-premises connectivity utilises VPN Gateway (up to 10 Gbps) or ExpressRoute (up to 100 Gbps) in the hub VNet. Border Gateway Protocol (BGP) advertisements propagate on-premises routes to all spoke VNets automatically. For high-availability scenarios, organisations deploy dual ExpressRoute circuits or ExpressRoute with VPN failover, leveraging Azure’s resilience building blocks including Availability Zones and Region Pairs to ensure maximum uptime for mission-critical connectivity.
Security Architecture:
Azure Firewall Premium or third-party NVAs (Palo Alto VM-Series, Fortinet FortiGate, Check Point CloudGuard) deployed in the hub inspect all inter-spoke and north-south traffic. Network Security Groups (NSGs) provide subnet-level access control in both hub and spokes, whilst Application Security Groups (ASGs) enable identity-based network policies.
Private endpoints for Azure PaaS services typically deploy in spoke VNets, with private DNS zones centralised in the hub for resolution management. This pattern ensures spoke workloads access services like Azure SQL Database, Storage Accounts, and Key Vault over Microsoft’s backbone network without internet exposure.
Scalability Considerations:
Hub-spoke architectures scale vertically to approximately 200-500 VNets before management complexity becomes prohibitive. Each VNet peering consumes resources from Azure’s peering quotas (500 peerings per VNet), though in practice, operational management challenges emerge long before technical limits. Organisations with 50+ spokes typically implement automation using Terraform or Bicep templates to maintain consistent configurations.
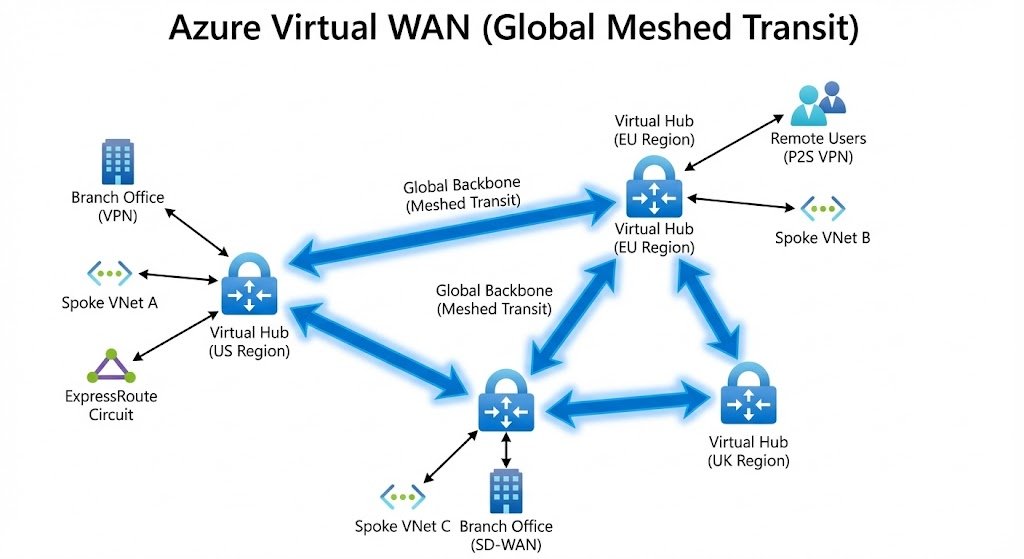
Azure Virtual WAN: Cloud-Native Global Transit
Azure Virtual WAN transforms traditional networking by providing a managed global transit architecture with built-in routing intelligence. Rather than manually configuring peering relationships and route tables, Virtual WAN offers an abstraction layer that simplifies complex topologies whilst enabling advanced scenarios like Any-to-Any connectivity across branches, VNets, and users.
Core Architecture Components:
A Virtual WAN deployment centres on Virtual Hubs, Microsoft-managed transit hubs deployed per region. Each Virtual Hub provides a fully meshed connectivity fabric supporting VNet connections, VPN connections, ExpressRoute circuits, and point-to-site VPN users. Microsoft manages the underlying infrastructure, including route tables, gateways, and high-availability configurations.
Organisations deploy multiple Virtual Hubs for multi-region architectures, with Microsoft automatically establishing hub-to-hub connectivity for global transit. A three-region deployment (UK South, West Europe, East US) creates a fully meshed backbone where VNets in any region can communicate with VNets, branches, or users in any other region through optimised routing.
Routing Intelligence:
Virtual WAN implements intent-based routing through routing policies rather than explicit route tables. Connection types (VNet, branch VPN, ExpressRoute, user VPN) associate with routing tables (Default, None, or custom), enabling sophisticated traffic segmentation. For example, isolating development VNets from production whilst maintaining connectivity between production VNets and ExpressRoute circuits requires only routing table associations, no manual route entries.
BGP communities automatically propagate routes between Virtual Hubs, enabling global transit scenarios. When a new branch office VPN connects to Virtual Hub UK South, routes automatically propagate to Virtual Hubs in West Europe and East US, making the branch reachable from all locations within minutes.
Integrated Security:
Azure Firewall deploys directly into Virtual Hubs (Secured Virtual Hub configuration), creating an integrated firewall-as-a-service model. Traffic between VNets, branches, and users automatically routes through the firewall based on routing intent policies. This eliminates complex UDR management required in traditional hub-spoke deployments.
Third-party security solutions integrate through Network Virtual Appliance (NVA) in Virtual Hub capability, allowing organisations to deploy Palo Alto, Fortinet, or Check Point directly into the Virtual WAN fabric. These NVAs participate in Virtual WAN routing, providing inspection services whilst maintaining the management simplicity of Virtual WAN.
SD-WAN Integration:
Virtual WAN excels at integrating with SD-WAN solutions through partnerships with vendors like Cisco, VMware, and Barracuda. SD-WAN appliances in branch offices establish encrypted tunnels to Virtual WAN VPN gateways, creating an overlay network that optimises traffic routing based on application requirements, link quality, and cost.
This integration enables scenarios where SaaS traffic (Microsoft 365, Salesforce) breakout locally at branches whilst corporate application traffic (Azure-hosted ERP systems) routes through Virtual WAN to Azure VNets. The SD-WAN controller manages policies whilst Virtual WAN handles Azure-side routing and connectivity.
Performance Characteristics:
Virtual WAN provides aggregate throughput up to 20 Gbps per Virtual Hub VPN gateway and 100 Gbps per ExpressRoute gateway. Multiple gateway instances provide scale-out capacity, with Microsoft managing load distribution. Inter-region VNet-to-VNet traffic within Virtual WAN utilises Microsoft’s global backbone with typical latencies of 2-5ms intra-region and 20-150ms inter-region depending on geographic distance.
Azure Virtual Network Manager: Centralised Management at Scale
Azure Virtual Network Manager (AVNM) provides centralised network topology and security policy management for VNets at scale, without requiring the full architectural shift to Virtual WAN. AVNM targets organisations seeking better management tooling for hub-spoke or mesh topologies whilst maintaining granular control over routing and connectivity.
Management Scope and Architecture:
AVNM operates through Network Manager instances that define management scope across subscriptions and management groups. A single Network Manager can manage thousands of VNets across an entire enterprise, applying consistent connectivity and security policies. Multiple Network Managers can co-exist for different organisational boundaries (production vs non-production, regional segmentation, business unit isolation).
Network Groups provide dynamic VNet grouping based on tags, names, or explicit membership. For example, an “EU-Production” Network Group might include all VNets in European regions tagged with “Environment: Production.” These groups become targets for connectivity and security policies, enabling template-based management at scale.
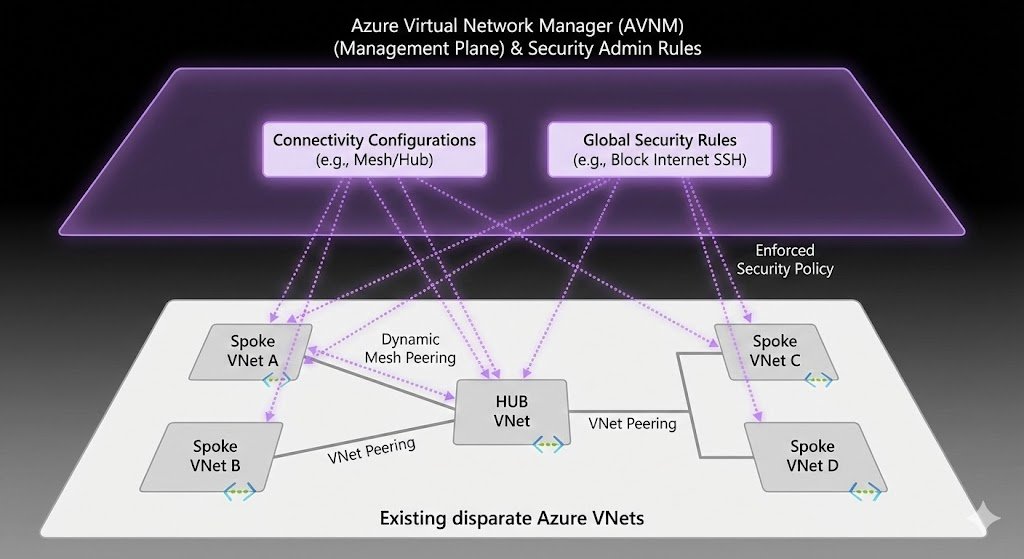
Connectivity Configurations:
AVNM supports two connectivity topologies: Hub-and-Spoke and Mesh. Hub-and-Spoke configurations define a hub VNet with automatic peering to spoke VNets in Network Groups, replicating traditional hub-spoke topology but with centralised management. AVNM automatically creates and maintains VNet peerings, eliminating manual configuration for each spoke addition.
Mesh configurations create full-mesh connectivity between all VNets in a Network Group, enabling direct spoke-to-spoke communication without hub transit. This topology suits scenarios requiring low-latency spoke-to-spoke connectivity whilst maintaining the security and management benefits of Network Groups. Regional mesh configurations reduce cross-region traffic costs by keeping intra-region traffic local.
Security Admin Rules:
Security Admin Rules represent AVNM’s killer feature for enterprises with complex security requirements. These rules deploy globally across Network Groups, operating at a higher priority than Network Security Groups (NSGs). Organisations enforce non-negotiable security policies (deny inbound RDP from internet, require specific IP ranges for management access) that subscription owners cannot override.
Security Admin Rules support priorities 1-4096, always evaluated before NSG rules. A global “Deny All Inbound from Internet” rule set at priority 100 applies across thousands of VNets, ensuring consistent security baseline regardless of individual NSG configurations. This addresses a common gap in large organisations where decentralised teams manage their own NSGs, potentially creating security inconsistencies.
Integration with Hub-Spoke:
AVNM complements rather than replaces traditional hub-spoke architectures. Organisations deploy AVNM to manage the hub-spoke topology (automated peering, global security policies) whilst maintaining hub-deployed firewalls and gateways for traffic inspection and on-premises connectivity. This provides the management benefits of centralisation without forcing architectural changes.
For organisations with existing hub-spoke deployments, AVNM adoption requires no downtime. Network Managers can import existing VNet peerings, taking over management without disrupting traffic. Security Admin Rules deploy alongside existing NSGs, adding additional protection layers rather than replacing existing security controls.
Deployment Models:
AVNM supports deployment across Azure regions with regional availability of Network Managers ensuring service continuity. A Network Manager deployed in UK South manages VNets across all Azure regions, with configuration data replicated for high availability. Policy deployment takes 10-15 minutes on average, with a goal state architecture ensuring eventual consistency across managed VNets.
Architectural Comparison and Decision Framework

Feature Comparison Matrix
| Capability | Hub-Spoke | Virtual WAN | Azure Virtual Network Manager |
|---|---|---|---|
| Connectivity Model | Manual peering | Managed global transit | Centralised peering management |
| Maximum VNet Scale | 200-500 (practical limit) | 2,000+ per region | 10,000+ |
| Spoke-to-Spoke Traffic | Through hub (adds 2-3ms) | Direct or via Secured Hub | Direct (mesh) or via hub |
| Multi-Region Transit | Manual configuration | Automatic hub-to-hub | Manual configuration |
| SD-WAN Integration | Third-party NVA required | Native integration | Third-party NVA required |
| Branch Connectivity | Site-to-site VPN | Optimised with routing intent | Site-to-site VPN |
| Security Integration | NVA or Azure Firewall in hub | Secured Virtual Hub | NVA or Azure Firewall in hub |
| Global Security Policies | Manual replication | Routing intent policies | Security Admin Rules |
| Management Complexity | High (100+ VNets) | Low (automated) | Medium (policy-based) |
| Configuration Time | 30-60 min per VNet | 10-15 min per connection | 5-10 min per Network Group |
| BGP Support | Full control | Managed by Microsoft | Full control |
| Cost Model | Pay per peering + NVA | Pay per hub + data processed | Pay per policy deployment |
| Operational Model | DIY management | Managed service | Policy-driven management |
When to Choose Hub-Spoke
Hub-spoke architecture remains the optimal choice for organisations requiring maximum control over routing, filtering, and security policy enforcement at the network layer. Financial services firms subject to stringent regulatory requirements often mandate hub-spoke for its explicit traffic paths and well-understood security boundaries.
Ideal Scenarios:
- 10-50 VNets with straightforward connectivity requirements
- Strong preference for third-party NVAs (Palo Alto, Fortinet) with advanced features
- Existing operational expertise in traditional networking
- Regulatory requirements for explicit traffic logging at network layer
- Cost sensitivity with limited multi-region requirements
- Need for granular control over BGP routing and route propagation
Manufacturing organisation with 30 VNets across three Azure regions, on-premises data centres via ExpressRoute, and existing Palo Alto firewall investment benefits from hub-spoke’s straightforward architecture. The operations team understands firewall routing, security policies deploy through familiar tooling, and annual networking costs remain predictable at £24,000-£36,000 depending on firewall instance sizing.
When to Choose Virtual WAN
Virtual WAN targets organisations with complex connectivity requirements spanning multiple Azure regions, branch offices, remote users, and integrated SD-WAN infrastructure. Retail organisations with hundreds of store locations and global logistics operations represent ideal Virtual WAN candidates.
Ideal Scenarios:
- 50+ VNets requiring Any-to-Any connectivity
- 20+ branch office locations requiring optimised Azure connectivity
- Existing SD-WAN deployment (Cisco Viptela, VMware SD-WAN)
- Multi-region Azure presence requiring global transit
- Remote user VPN at scale (1,000+ concurrent users)
- Limited networking operations team (preferring managed service)
Global retailer with 200+ store locations, Azure VNets in five regions, and requirement for store-to-Azure and store-to-store connectivity leverages Virtual WAN’s SD-WAN integration. Branch traffic optimises automatically based on Azure routing intelligence, new stores connect within minutes through SD-WAN orchestration, and centralised security policies apply globally. Annual costs of £180,000-£240,000 justify themselves through operational efficiency and reduced WAN circuit costs.
When to Choose Azure Virtual Network Manager
AVNM suits organisations operating at scale (50+ VNets) without complex SD-WAN requirements or multi-region transit needs. Technology companies with development, testing, and production environments across multiple subscriptions benefit from AVNM’s centralised management without Virtual WAN’s cost premium.
Ideal Scenarios:
- 50-500 VNets requiring consistent security policies
- Hub-spoke or mesh topology preference
- Decentralised subscription management requiring central guardrails
- Cost optimisation priority (40-60% less than Virtual WAN for intra-Azure scenarios)
- Security compliance requirements for global policy enforcement
- Existing hub-spoke deployment requiring better management tooling
Software-as-a-service provider with 120 VNets across customer environments, development stages, and regions utilises AVNM for centralised security admin rules ensuring compliance whilst allowing development teams autonomy within boundaries. Network Groups organise VNets by customer and environment, connectivity policies automate peering, and security rules enforce requirements like “no RDP from internet” globally. Annual costs of £18,000-£28,000 represent 65% savings compared to equivalent Virtual WAN deployment.
Hybrid Approaches
Many enterprises operate hybrid architectures combining strengths of multiple approaches. Common patterns include:
Hub-Spoke with AVNM: Traditional hub-spoke topology for traffic inspection and on-premises connectivity, with AVNM adding centralised policy management and automated peering. This approach provides maximum flexibility at moderate cost, suitable for 50-200 VNet deployments where Virtual WAN costs cannot be justified.
Regional Virtual WAN with Hub-Spoke Spokes: Virtual WAN Virtual Hubs serve as inter-region transit points and branch connectivity aggregators, with traditional hub-spoke topologies within each region for workload connectivity. This pattern optimises costs by using Virtual WAN for scenarios where it adds clear value (branch connectivity, global transit) whilst maintaining hub-spoke’s lower per-VNet costs within regions.
Virtual WAN with AVNM Security Policies: Virtual WAN handles connectivity and routing, with AVNM Security Admin Rules enforcing global security policies across all VNet connections. This ensures consistent security baseline whilst leveraging Virtual WAN’s routing intelligence.
Cost Analysis: 10, 50, and 200+ VNet Scenarios
10 VNet Deployment: Small-to-Medium Enterprise
A small-to-medium enterprise operating 10 VNets across 2 Azure regions (UK South, West Europe) with on-premises connectivity via ExpressRoute faces the following monthly costs:
Hub-Spoke Architecture:
- VNet peering (10 spokes × £7 per peering × 2 for bidirectional): £140/month
- Azure Firewall Standard (2 instances for HA): £620/month
- ExpressRoute Gateway (Standard): £210/month
- Data processing (estimated 1TB ingress, 2TB egress): £150/month
- Total: £1,120/month (£13,440/year)
Virtual WAN:
- Virtual Hub (2 regions × £175/month base): £350/month
- VNet connections (10 × £15): £150/month
- ExpressRoute Gateway: £210/month
- Data processing (3TB × £7.5/GB): £225/month
- Secured Virtual Hub (Azure Firewall Premium): £1,040/month
- Total: £1,975/month (£23,700/year)
Hub-Spoke with AVNM:
- VNet peering: £140/month
- Azure Firewall Standard (2 instances): £620/month
- ExpressRoute Gateway: £210/month
- AVNM (10 VNets in managed scope): £20/month
- Data processing: £150/month
- Total: £1,140/month (£13,680/year)
Analysis: At 10 VNet scale, traditional hub-spoke remains most cost-effective, with Virtual WAN costing 76% more annually. AVNM adds minimal cost (£240/year) whilst providing centralised management benefits. Virtual WAN’s cost premium cannot be justified unless specific features (SD-WAN integration, branch connectivity) are required. Organisations implementing comprehensive FinOps practices for cloud cost management typically establish decision frameworks evaluating both direct infrastructure costs and operational efficiency gains.
50 VNet Deployment: Mid-Market Enterprise
An organisation with 50 VNets across 3 Azure regions (UK South, West Europe, East US), 10 branch office locations, and 500 remote users:
Hub-Spoke Architecture:
- VNet peering (50 spokes × £7 × 2): £700/month
- Azure Firewall Premium (3 regions × 2 for HA): £3,120/month
- ExpressRoute Gateway (3 regions): £630/month
- VPN Gateway for branches (3 regions): £360/month
- Point-to-site VPN users: £140/month
- Data processing (estimated 10TB): £750/month
- Management overhead (estimated 40 hours/month × £50/hour): £2,000/month
- Total: £7,700/month (£92,400/year)
Virtual WAN:
- Virtual Hubs (3 regions × £175): £525/month
- VNet connections (50 × £15): £750/month
- Site-to-site VPN (10 branches × £20): £200/month
- Point-to-site VPN users: £140/month
- ExpressRoute Gateway: £630/month
- Secured Virtual Hubs (3 × £1,040): £3,120/month
- Data processing (10TB × £7.5/GB): £750/month
- Management overhead (reduced to 10 hours/month): £500/month
- Total: £6,615/month (£79,380/year)
Hub-Spoke with AVNM:
- VNet peering: £700/month
- Azure Firewall Premium (6 instances): £3,120/month
- ExpressRoute Gateway: £630/month
- VPN Gateway: £360/month
- Point-to-site VPN: £140/month
- AVNM (50 VNets): £100/month
- Data processing: £750/month
- Management overhead (20 hours/month): £1,000/month
- Total: £6,800/month (£81,600/year)
Analysis: At 50 VNet scale with branch connectivity requirements, Virtual WAN becomes cost-competitive due to reduced management overhead (£18,000/year savings). The £79,380 annual cost undercuts traditional hub-spoke’s £92,400, primarily through operational efficiency. AVNM with hub-spoke provides middle-ground at £81,600, suitable for organisations without significant branch connectivity needs.
200+ VNet Deployment: Enterprise Scale
Large enterprise with 200 VNets across 5 Azure regions globally, 50 branch offices, 2,000 remote users, and multi-region ExpressRoute:
Hub-Spoke Architecture:
- VNet peering (200 × £7 × 2): £2,800/month
- Azure Firewall Premium (10 instances): £5,200/month
- ExpressRoute Gateway (5 regions): £1,050/month
- VPN Gateway (5 regions): £600/month
- Point-to-site VPN users: £280/month
- Data processing (50TB): £3,750/month
- Management overhead (estimated 160 hours/month): £8,000/month
- Total: £21,680/month (£260,160/year)
Virtual WAN:
- Virtual Hubs (5 regions × £175): £875/month
- VNet connections (200 × £15): £3,000/month
- Site-to-site VPN (50 branches × £20): £1,000/month
- Point-to-site VPN users: £280/month
- ExpressRoute Gateway: £1,050/month
- Secured Virtual Hubs (5 × £1,040): £5,200/month
- Data processing (50TB × £7.5/GB): £3,750/month
- Management overhead (40 hours/month): £2,000/month
- Total: £17,155/month (£205,860/year)
Hub-Spoke with AVNM:
- VNet peering: £2,800/month
- Azure Firewall Premium (10 instances): £5,200/month
- ExpressRoute Gateway: £1,050/month
- VPN Gateway: £600/month
- Point-to-site VPN: £280/month
- AVNM (200 VNets): £400/month
- Data processing: £3,750/month
- Management overhead (80 hours/month): £4,000/month
- Total: £18,080/month (£216,960/year)
Analysis: At enterprise scale (200+ VNets), Virtual WAN’s operational efficiency generates £54,300 annual savings compared to traditional hub-spoke (21% reduction). AVNM with hub-spoke reduces management overhead by 50% compared to pure hub-spoke, delivering £43,200 annual savings whilst maintaining architectural control. Virtual WAN justifies its premium through automated global transit, reduced operational burden, and integrated SD-WAN capabilities critical at this scale.
Hidden Cost Considerations
Beyond direct infrastructure costs, organisations must evaluate:
Skills and Training: Virtual WAN requires Azure-specific networking knowledge rather than traditional networking expertise. Budget £10,000-£20,000 annually for training and certification programmes. Hub-spoke leverages existing networking skills, reducing training investment.
Management Tooling: Infrastructure-as-Code complexity varies significantly. Hub-spoke requires comprehensive Terraform or Bicep modules managing peerings, route tables, and NSGs. Virtual WAN simplifies to connection objects and routing policies. AVNM introduces policy-based management requiring different automation approaches.
Data Transfer Costs: Inter-region VNet-to-VNet traffic costs £0.02/GB for both hub-spoke and Virtual WAN within the same networking construct. However, Virtual WAN’s routing intelligence can optimise paths, potentially reducing costs for scenarios with complex inter-region communication patterns.
Disaster Recovery: Hub-spoke architectures require explicit DR planning for hub VNet failures. Virtual WAN’s managed service provides built-in redundancy. Factor £2,000-£5,000 annually for DR testing and validation in hub-spoke deployments.
Security and Performance Trade-Offs
Security Architecture Comparison
Defence in Depth Layers:
Hub-spoke architectures provide explicit security layers through network topology. Traffic between spokes always traverses hub-deployed firewalls, enabling deep packet inspection, intrusion detection/prevention, and comprehensive logging. Security teams maintain complete visibility into east-west traffic patterns, with firewall logs capturing every inter-spoke communication.
Virtual WAN’s Secured Virtual Hub configuration embeds Azure Firewall directly into the transit fabric, inspecting traffic based on routing intent. This approach simplifies configuration (no manual UDRs) but reduces flexibility for third-party NVA features like advanced threat detection or custom security applications. Organisations requiring specialised security appliances deploy NVA in Virtual Hub at additional complexity and cost.
AVNM Security Admin Rules operate at a different layer than firewalls, providing deny-list capabilities that complement rather than replace firewall inspection. Rules like “deny all inbound RDP from internet” or “require source IP in corporate range for management traffic” enforce non-negotiable baselines across thousands of VNets, preventing subscription owners from creating security gaps through permissive NSG configurations.
Zero Trust Implementation:
Modern zero trust architectures emphasise identity-based access, micro-segmentation, and least-privilege principles. Hub-spoke topologies implement zero trust through network segmentation (isolated spokes), identity-aware firewalls (Azure Firewall Premium with TLS inspection), and private endpoint architectures preventing public internet exposure.
Virtual WAN enhances zero trust through routing intent policies that automatically isolate traffic flows based on business requirements. Development VNets connecting to one routing table, production to another, creates logical segmentation without complex NSG management. Integration with Azure Active Directory conditional access enables user VPN access tied to device compliance and user risk levels.
AVNM Security Admin Rules provide the governance layer essential for zero trust at scale. Global policies like “all VNets must deny SSH from internet except management subnet” or “specific IP ranges required for administrative access” enforce consistently across decentralised teams, preventing security policy drift that undermines zero trust implementations.
Compliance and Regulatory Requirements:
Financial services organisations subject to PCI-DSS, FCA regulations, or SWIFT CSP requirements typically favour hub-spoke architectures for their explicit network boundaries and comprehensive logging capabilities. Auditors understand traditional network topologies, with clear demarcation between trusted, untrusted, and DMZ zones.
Virtual WAN presents challenges for organisations with strict regulatory requirements around network segmentation evidence. Whilst technically providing equivalent security, the abstraction of routing into Microsoft-managed infrastructure can complicate compliance documentation. Forward-thinking auditors increasingly accept Virtual WAN, but organisations should validate acceptance with auditors before committing to migrations.
Healthcare organisations managing protected health information under GDPR and NHS Digital requirements successfully deploy all three architectures, provided proper encryption (ExpressRoute with MACsec, VPN with IKEv2), access controls (RBAC limiting network configuration), and audit logging (Azure Monitor logs, firewall logs forwarded to SIEM) are implemented consistently.
Performance Characteristics and Latency
Intra-Region Communication:
Direct VNet peering provides the lowest latency path for spoke-to-spoke communication, typically 0.5-1ms within the same Azure region. Hub-spoke architectures add 2-3ms due to firewall inspection and hub transit. For latency-sensitive workloads (high-frequency trading platforms, real-time gaming backends, IoT telemetry processing), this difference impacts application performance.
Virtual WAN spoke-to-spoke traffic within the same Virtual Hub can route directly (no firewall) or through Secured Virtual Hub (with inspection), depending on routing intent configuration. Direct routing matches VNet peering latency, whilst inspected traffic adds 2-3ms similar to traditional hub-spoke. The key difference: routing intent configuration changes dynamically without modifying VNet configurations.
AVNM mesh configurations enable direct spoke-to-spoke connectivity with <1ms latency whilst maintaining centralised security policy management. Organisations requiring ultra-low latency for specific workload groups (database clusters, Kubernetes node pools, high-performance computing) deploy mesh connectivity configurations whilst maintaining hub-spoke for other workloads.
Inter-Region Performance:
Azure’s backbone network provides 20-150ms latency between regions depending on geographic distance (UK South to West Europe: 20-25ms; UK South to Australia East: 140-160ms). Hub-spoke inter-region traffic requires careful route table configuration to optimise paths, often traversing ExpressRoute or VPN gateways unnecessarily.
Virtual WAN optimises inter-region routing automatically through hub-to-hub connections over Microsoft’s backbone. A VNet in UK South communicating with a VNet in East US routes through Virtual Hub UK South → Virtual Hub East US → destination VNet, following the optimal backbone path. This automation eliminates routing misconfigurations that inadvertently hairpin traffic through ExpressRoute circuits or on-premises networks.
Monitoring data from enterprises operating global Virtual WAN deployments shows average latency reductions of 15-25% compared to traditional hub-spoke architectures, primarily by eliminating routing inefficiencies and leveraging Microsoft’s backbone network effectively.
Throughput and Scale:
Hub-spoke throughput limits depend on firewall/NVA performance and VNet peering bandwidth. Azure Firewall Premium provides up to 100 Gbps throughput with Premium SKU, whilst VNet peering supports unlimited bandwidth within regions (Microsoft doesn’t publish hard limits). Third-party NVAs scale from 1-45 Gbps depending on instance size and vendor.
Virtual WAN Virtual Hub gateways scale to 20 Gbps per VPN gateway instance and 100 Gbps per ExpressRoute gateway instance. Multiple gateway instances provide scale-out capacity. VNet-to-VNet traffic within Virtual WAN leverages Microsoft’s backbone without explicit throughput limits beyond physical infrastructure capabilities.
Real-world testing by organisations processing high-volume data transfer (media encoding, financial data aggregation, scientific computing) demonstrates sustainable throughput of 40-60 Gbps through Virtual WAN Virtual Hubs, significantly exceeding single NVA capacity in traditional hub-spoke deployments.
Security Incident Response
Monitoring and Visibility:
Hub-spoke architectures centralise monitoring through hub-deployed firewalls and Network Watcher. Azure Firewall logs integrate with Azure Monitor, Log Analytics, and SIEM solutions, providing comprehensive visibility into network traffic patterns, denied connections, and threat indicators. Network Watcher traffic analytics reveal spoke-to-spoke communication patterns, top talkers, and anomalous behaviours.
Virtual WAN Secured Virtual Hubs provide equivalent logging capabilities through embedded Azure Firewall, with additional routing insights through Virtual WAN connection monitor. Organisations gain visibility into which branches, VNets, and users generate traffic volumes, latency patterns, and connectivity failures. The integrated view simplifies troubleshooting compared to hub-spoke’s distributed logging across multiple hubs.
AVNM doesn’t directly provide logging (it’s a management plane service), but Security Admin Rules violations appear in Azure Activity Logs and NSG flow logs. Organisations implement Azure Policy alongside AVNM to audit compliance with security configurations and detect attempts to bypass Security Admin Rules through service principal manipulation or elevated permissions.
Incident Isolation:
Traditional hub-spoke topologies enable rapid incident isolation by modifying UDRs or NSG rules on affected spokes. A compromised spoke gets disconnected from other spokes within minutes by removing its peering or adjusting hub firewall rules. This explicit control appeals to security operations teams familiar with traditional network isolation procedures.
Virtual WAN isolation requires routing policy changes rather than physical disconnection. Security teams modify routing table associations, moving compromised VNets to isolated routing tables without hub connectivity. Whilst effective, this approach requires different operational procedures and tooling compared to traditional networking.
AVNM Security Admin Rules provide preventive isolation through policies like “VNets in Development network group cannot initiate connections to Production network group.” These rules deploy proactively, preventing lateral movement scenarios that require reactive isolation during incidents.
Migration Paths from On-Premises Networks
From Traditional Data Centre to Azure Hub-Spoke
Assessment Phase (Weeks 1-4):
Network discovery mapping existing on-premises architecture including MPLS networks, data centre interconnects, firewall policies, and application dependencies. Tools like Azure Migrate Network Assessment analyse current state, identifying IP address space conflicts, routing protocols in use, and bandwidth requirements.
Organisations typically discover 20-40% of IP address space requires renumbering to avoid conflicts with Azure VNet ranges. Plan address space allocation across hub (typically /22), spokes (typically /24 or /23), and reserved space for future growth. Document existing firewall rules, grouping by security zones (DMZ, trusted, management) for migration into Azure NSGs and Azure Firewall policies.
Pilot Implementation (Weeks 5-12):
Deploy hub VNet in production subscription with ExpressRoute gateway, Azure Firewall, and management services. Establish ExpressRoute connectivity to on-premises, validating BGP route propagation and testing connectivity from on-premises to hub VNet. Many organisations encounter BGP AS path issues or route filtering problems during this phase, requiring collaboration with network carriers and Microsoft support.
Migrate first spoke workload (typically non-production application) with minimal external dependencies. This pilot validates migration procedures, identifies tooling gaps, and trains operations teams. Common issues include DNS resolution (requiring Azure Private DNS zones), authentication dependencies (on-premises Active Directory), and network security appliance compatibility (requiring network virtual appliance evaluation).
Production Migration (Months 4-12):
Phased application migration following dependency mapping. Applications with minimal on-premises dependencies migrate first, establishing patterns for database migration (Azure Database Migration Service), file storage migration (AzCopy, Data Box), and application refactoring for cloud-native services.
Organisations typically migrate 20-30% of workloads in months 4-6, 50-60% by month 9, with remaining 10-20% requiring extensive refactoring or remaining on-premises due to licensing, latency, or compliance constraints. Network bandwidth requirements peak during data migration phases, often necessitating temporary ExpressRoute bandwidth increases or parallel circuits.
Hybrid Steady State (Ongoing):
Many enterprises maintain hybrid hub-spoke architectures indefinitely, with on-premises data centres hosting workloads unsuitable for cloud migration (mainframes, specialised hardware, ultra-low-latency trading systems). Azure hub VNet becomes an extension of the corporate network, with ExpressRoute providing seamless connectivity between environments.
From Hub-Spoke to Virtual WAN
Planning and Design (Weeks 1-6):
Virtual WAN migration planning addresses routing changes, connectivity model shifts, and operational procedure updates. Key decisions include Virtual Hub placement (which Azure regions), routing table design (isolated or shared connectivity), and security integration approach (Secured Virtual Hub or third-party NVA).
Create detailed mapping between existing hub-spoke architecture and target Virtual WAN configuration. Hub VNet firewall policies map to Virtual Hub routing intent and Azure Firewall policies. Spoke VNet peerings transform into Virtual Hub VNet connections. ExpressRoute and VPN connections move from hub gateways to Virtual Hub gateways.
Parallel Deployment (Weeks 7-14):
Build Virtual WAN infrastructure parallel to existing hub-spoke, avoiding disruption to production workloads. Deploy Virtual Hubs in each region, configure routing intent, establish Secured Virtual Hubs, and migrate ExpressRoute circuits using circuit authorisation keys. This parallel approach enables testing and validation before cutover.
Begin connecting non-production spoke VNets to Virtual Hubs, validating connectivity to other VNets, branches, and on-premises networks. Test application functionality, performance, and security policy enforcement. Many organisations discover routing policy misconfigurations during this phase, requiring iteration before production migration.
Cutover Execution (Weeks 15-26):
Production workload migration follows application dependency groups. Applications communicating primarily with other Azure VNets migrate first, leveraging Virtual WAN’s optimised routing. Applications with heavy on-premises dependencies migrate later, after ExpressRoute circuits successfully transition to Virtual Hubs.
Expect 4-8 hour maintenance windows per application group for network cutover. Remove VNet peerings to old hub, connect VNets to Virtual Hub, validate routing, and test application functionality. Monitoring during cutover focuses on ExpressRoute route propagation, Virtual Hub routing table state, and application health checks.
Decommissioning (Weeks 27-32):
After validating production workloads in Virtual WAN, decommission old hub-spoke infrastructure. Remove hub VNet gateways (triggering ExpressRoute deallocations), delete hub VNet peerings, and eliminate hub VNet infrastructure. Organisations typically reclaim 30-40% of network infrastructure costs through hub decommissioning and operational simplification.
From Hub-Spoke to AVNM-Managed Hub-Spoke
AVNM Onboarding (Weeks 1-4):
AVNM adoption requires no network architecture changes, minimising risk and disruption. Deploy Network Manager instance, define management scope across subscriptions and management groups, and create initial Network Groups based on VNet tagging strategy.
Import existing VNet peerings into AVNM connectivity configurations, transferring management from individual peerings to centralised policy. This import process maintains existing connectivity whilst enabling centralised management going forward. Test connectivity thoroughly, ensuring no disruption during management transfer.
Policy Implementation (Weeks 5-10):
Deploy Security Admin Rules incrementally, starting with deny-list policies that don’t impact legitimate traffic (deny inbound RDP from internet, block known malicious IPs). Monitor Azure Activity Logs for Security Admin Rule violations, identifying overly restrictive policies before they disrupt operations.
Gradually implement allow-list policies for management traffic (require source IP in corporate range for administrative protocols), validation through testing in non-production environments first. Many organisations discover legitimate management traffic from unexpected source IPs during this phase, requiring policy refinement.
Operational Transition (Ongoing):
Shift network management procedures from individual VNet operations to policy-driven management through Network Managers. Teams request VNet additions through Network Group memberships rather than manual peering configurations. Security teams enforce policies through Security Admin Rules rather than attempting to govern hundreds of individual NSG configurations.
This operational transformation delivers the primary benefit of AVNM: reducing management overhead whilst maintaining hub-spoke’s architectural control and cost characteristics. Organisations report 60-70% reduction in network configuration time within 3-6 months of AVNM adoption.
Real-World Case Studies
HSBC: Global Financial Services on Virtual WAN
HSBC operates over 5,000 Kubernetes clusters across four cloud providers, with Azure playing a central role in the bank’s hybrid cloud strategy. The organisation implemented Azure Virtual WAN to manage connectivity across 40+ Azure regions, integrating with existing MPLS networks and SD-WAN infrastructure serving thousands of branch offices globally.
Implementation Scale:
- 40+ Azure regions with Virtual WAN deployment
- 2,000+ Azure VNets connected to Virtual Hubs
- 3,500+ branch offices connecting via SD-WAN integration
- 50,000+ remote users via point-to-site VPN
Results:
- 90% reduction in network provisioning time (days to minutes for new connectivity)
- Automated global routing reducing manual configuration errors by 95%
- Unified security policy enforcement through Secured Virtual Hubs
- £2.4 million annual operational savings through reduced management overhead
Key Success Factors: HSBC’s phased implementation over 18 months, starting with non-production environments in a single region before expanding globally. The bank maintained parallel hub-spoke infrastructure during migration, enabling rollback if issues emerged. Deep integration with existing SD-WAN vendor (Cisco Viptela) proved critical for seamless branch connectivity.
Marks & Spencer: Retail Hub-Spoke with AVNM
Marks & Spencer, operating 1,400+ stores across the UK and international markets, manages an Azure footprint exceeding 200 VNets across development, testing, and production environments. The retailer implemented AVNM in 2023 to centralise network management whilst maintaining its existing hub-spoke architecture optimised for retail point-of-sale and supply chain applications.
Implementation Scope:
- 200+ Azure VNets across 5 regions
- Traditional hub-spoke topology with Palo Alto VM-Series firewalls
- AVNM Security Admin Rules enforcing PCI-DSS compliance requirements
- Network Groups organising VNets by environment and business function
Results:
- 65% reduction in network configuration time through automated peering
- 100% compliance enforcement for “no inbound RDP from internet” policy
- £180,000 annual savings compared to Virtual WAN alternative
- 2-hour maximum time for new VNet connectivity (previous: 2-3 days)
Key Success Factors: M&S leveraged existing hub-spoke investment, adding AVNM management layer without architectural disruption. Security Admin Rules enforcement proved crucial for PCI-DSS compliance across development teams with varying security maturity. The retailer’s decision to avoid Virtual WAN stemmed from limited requirement for branch connectivity (stores connect via existing retail WAN) and cost optimisation priorities.
NHS Digital: Healthcare Hybrid Architecture
NHS Digital manages critical national healthcare IT infrastructure serving NHS England, including patient record systems, appointment booking platforms, and clinical decision support tools. The organisation operates a hybrid architecture combining on-premises data centres with Azure, implementing hub-spoke topology with ExpressRoute connectivity to meet stringent NHS data security requirements.
Deployment Architecture:
- 120 Azure VNets across 3 UK regions
- Dual ExpressRoute circuits (10 Gbps each) providing redundant connectivity
- Azure Firewall Premium with TLS inspection for inbound/outbound traffic
- Private endpoints for all PaaS services (Azure SQL, Storage, Key Vault)
Security Requirements:
- NHS Data Security and Protection Toolkit compliance
- GDPR requirements for health data processing
- Cyber Essentials Plus certification
- Regular NHS Digital security assessments
Performance Outcomes:
- <10ms latency between Azure VNets and on-premises data centres via ExpressRoute
- 99.995% availability for ExpressRoute connectivity (5 minutes downtime annually)
- Zero security incidents related to network architecture in 24 months operation
- £840,000 annual cost vs estimated £1.2 million for equivalent Virtual WAN implementation
Lessons Learned: NHS Digital’s decision to maintain hub-spoke reflected regulatory clarity (auditors understand traditional network topologies) and existing operational expertise in Cisco networking. The organisation evaluated Virtual WAN but determined its primary benefits (SD-WAN integration, global transit) didn’t align with NHS’s hub-centric, UK-focused architecture. Future plans include AVNM adoption for improved policy management whilst maintaining hub-spoke foundation.
Vodafone: Telecommunications SD-WAN Integration
Vodafone leveraged Azure Virtual WAN to integrate its global telecommunications network with Azure cloud services, creating a unified network fabric spanning 180+ countries. The implementation enables Vodafone enterprise customers to access cloud services through optimised SD-WAN routing whilst maintaining security and performance SLAs.
Implementation Characteristics:
- 25+ Azure Virtual Hubs across global regions
- Integration with Vodafone’s proprietary SD-WAN platform
- 8,000+ enterprise customer connections via SD-WAN
- Any-to-Any connectivity between customers, cloud services, and data centres
Business Outcomes:
- 40% reduction in latency for customer-to-Azure traffic through routing optimisation
- 99.95% availability SLA for Virtual WAN connectivity
- £6 million annual cost avoidance through automated network provisioning
- New revenue streams from managed cloud connectivity services
Differentiating Factors: Vodafone’s telecommunications expertise positioned Virtual WAN as infrastructure extending existing network services rather than standalone Azure networking. The company developed custom SD-WAN integration leveraging Virtual WAN’s partner ecosystem, enabling sophisticated traffic engineering for enterprise customers with multi-cloud requirements.
Future Trends and Innovation
AI-Driven Network Optimisation
Azure networking services increasingly incorporate artificial intelligence for traffic pattern analysis, security threat detection, and automated optimisation recommendations. Azure Network Watcher’s Connection Monitor utilises machine learning to establish baseline network performance, detecting anomalies indicating connectivity degradation or security incidents.
Microsoft Research teams explore AI-driven routing optimisation that dynamically adjusts Virtual WAN routing policies based on application performance requirements, cost constraints, and real-time network conditions. Early prototypes demonstrate 15-30% cost reductions through intelligent traffic routing that directs latency-sensitive traffic via ExpressRoute whilst routing bulk data transfer through cheaper internet paths.
IPv6 and Dual-Stack Networking
Azure’s gradual IPv6 adoption reflects global internet protocol evolution. Virtual WAN supports IPv6 addressing for VNet connections, enabling organisations to prepare for IPv6 requirements without immediate IPv4 retirement. AVNM extends IPv6 support through security policies and connectivity management spanning both IP versions.
Organisations planning 3-5 year network roadmaps should architect for dual-stack operation, maintaining IPv4 compatibility whilst enabling IPv6 where beneficial. IoT deployments particularly benefit from IPv6’s vast address space, eliminating NAT complexity for device connectivity.
Edge Computing Integration
Azure’s edge computing strategy through Azure Stack Edge and Azure Stack HCI creates new networking requirements. Hub-spoke and Virtual WAN architectures extend to edge locations, with local VNets managed through AVNM policies ensuring consistent security and connectivity across distributed edge deployments.
Manufacturing sector early adopters deploy Azure Stack HCI in factories with local VNet connectivity to Azure hub VNets, enabling hybrid applications that process sensitive data locally whilst leveraging cloud analytics. These deployments favour hub-spoke patterns for their explicit control over edge-to-cloud traffic flows.
Quantum-Safe Cryptography
Quantum computing’s threat to current cryptographic standards drives preparation for quantum-safe networking. Microsoft actively develops post-quantum cryptographic algorithms for VPN and ExpressRoute encryption. Organisations architecting long-term network infrastructure should evaluate quantum-safe readiness, particularly for ExpressRoute with MACsec and VPN connections protecting sensitive data.
Sustainability and Carbon Optimisation
Cloud networking architecture decisions impact organisational carbon footprints. Virtual WAN’s routing optimisation reduces unnecessary data transfer across inefficient paths, decreasing carbon emissions from data centre operations. Microsoft publishes carbon intensity metrics for Azure regions, enabling organisations to architect for carbon efficiency alongside cost and performance.
Forward-thinking enterprises incorporate carbon metrics into network design decisions, preferring intra-region VNet communication over inter-region traffic, optimising ExpressRoute circuit sizing to match actual needs rather than overprovisioning, and leveraging Azure’s renewable energy commitments through data residency choices.
Strategic Recommendations
Start with Requirements, Not Technology
Organisations frequently approach Azure networking architecture with preconceived technology choices rather than comprehensive requirements analysis. This challenge is familiar to business leaders evaluating cloud computing investments, where technology decisions must align with organisational objectives rather than following industry trends. Begin with business requirements (application latency sensitivity, security compliance obligations, operational complexity tolerance, budget constraints) before selecting hub-spoke, Virtual WAN, or AVNM.
Critical Questions:
- How many VNINFO branch offices require Azure connectivity?
- What are security compliance requirements (PCI-DSS, HIPAA, FCA)?
- Does the organisation require multi-region transit?
- What is operational team’s networking expertise (traditional vs cloud-native)?
- What are budget constraints and cost optimisation priorities?
Answers to these questions naturally guide architecture selection. Fifty branch offices requiring optimised connectivity suggests Virtual WAN. Stringent regulatory requirements with traditional security team suggests hub-spoke. Large VNet footprint requiring centralised policy management suggests AVNM.
Adopt Phased Implementation
Network architecture migrations carry significant risk. Adopt phased implementation approaches that validate designs in non-production before production migration:
Phase 1 (Months 1-3): Pilot implementation with 5-10 non-production VNets, establishing patterns for connectivity, security, and monitoring.
Phase 2 (Months 4-9): Expand to additional non-production environments and first production workloads with minimal external dependencies.
Phase 3 (Months 10-18): Migrate remaining production workloads following dependency groups, maintaining parallel infrastructure until validation complete.
Phase 4 (Months 19-24): Optimise deployed architecture based on operational experience, implementing cost optimisations and security enhancements identified during operation.
Plan for Cost Optimisation
Network costs represent 10-20% of total Azure spending for typical enterprises. Implement continuous cost optimisation:
VNet right-sizing: Regularly review VNet address space allocation. Organisations commonly overprovision VNets with /16 address space when /24 suffices, complicating IP address management without benefit.
ExpressRoute circuit sizing: Monitor ExpressRoute utilisation quarterly. Circuits consistently operating <40% utilisation represent optimisation opportunities. Consider bandwidth reduction or circuit elimination if connectivity shifts to VPN.
Data transfer optimisation: Implement Azure Front Door or Traffic Manager to keep regional traffic local, reducing expensive inter-region data transfer. For workloads generating high egress (video streaming, large file downloads), evaluate Azure CDN to reduce origin bandwidth costs.
VNet peering consolidation: Organisations with complex spoke-to-spoke communication patterns benefit from mesh connectivity (via AVNM) rather than hub transit, eliminating firewall processing costs for traffic flows not requiring inspection.
Maintain Security Defence in Depth
Regardless of architecture selection, implement comprehensive security controls:
Network layer: NSGs on all subnets, Azure Firewall or third-party NVA for traffic inspection, DDoS Protection Standard for public-facing services.
Identity layer: Azure AD conditional access for user VPN, managed identities for service-to-service authentication, Key Vault for secrets management.
Data layer: Encryption at rest (Azure Storage encryption, SQL TDE), encryption in transit (TLS 1.2+ required), private endpoints eliminating public internet exposure.
Monitoring layer: Azure Monitor logging all network flows, Security Centre detecting anomalous behaviours, Sentinel providing SIEM analysis and automated response.
Key Pitfalls to Avoid
Over-architecting for theoretical requirements: Organisations implement Virtual WAN for “future multi-region requirements” that never materialise, spending unnecessarily compared to hub-spoke with planned migration path.
Underestimating operational impact: Technology selections require operational capability. Virtual WAN’s automation benefits assume Azure-native skills. Organisations lacking cloud expertise may find hub-spoke’s familiarity outweighs Virtual WAN’s theoretical advantages.
Ignoring migration complexity: Network architecture migrations impact all applications simultaneously. Underestimating migration complexity, particularly for applications with tight latency requirements or complex DNS dependencies, leads to extended outages and project failures.
Neglecting cost management: Initial architecture deployments often overprovision resources “to be safe.” Without regular cost reviews, organisations perpetuate expensive configurations that could be optimised without impacting functionality.
Implementation Action Plan
Immediate Actions (This Week):
- Document current network architecture (on-premises and existing Azure)
- Identify pain points (management complexity, security gaps, cost concerns)
- Engage stakeholders across networking, security, applications, and finance teams
- Establish project governance and decision-making framework
Short-Term Actions (Months 1-3):
- Complete comprehensive requirements analysis across business and technical dimensions
- Design target architecture with clear justification for hub-spoke, Virtual WAN, or AVNM selection
- Develop migration plan with phased approach and rollback procedures
- Establish success metrics (cost reduction targets, performance SLAs, security compliance)
- Deploy pilot implementation for validation
Medium-Term Actions (Months 4-12):
- Execute production migration following validated patterns from pilot
- Implement monitoring and cost management dashboards
- Train operations teams on new architecture patterns and troubleshooting procedures
- Document architecture decisions, operational runbooks, and troubleshooting guides
- Conduct post-implementation review against success metrics
Long-Term Actions (12+ Months):
- Continuous optimisation based on operational experience and cost analysis
- Regular architecture reviews (quarterly) to validate alignment with business requirements
- Evaluate emerging Azure networking capabilities for potential adoption
- Refine security policies based on threat landscape changes
- Plan for next-generation networking requirements (edge computing, IoT, quantum-safe cryptography)
Azure networking architecture represents a strategic decision with multi-year implications for costs, security, and operational efficiency. Hub-spoke provides maximum control and familiarity for organisations with traditional networking expertise. Virtual WAN delivers management simplicity and advanced features for complex global deployments. AVNM offers centralised policy management at hub-spoke costs for organisations operating at scale.
Success requires comprehensive requirements analysis, realistic assessment of operational capabilities, and commitment to phased implementation with continuous optimisation. Organisations making informed architecture selections based on business requirements rather than technology trends position themselves for efficient, secure, and cost-effective cloud networking that supports business objectives for years to come.
Useful Links
- Azure Virtual WAN Documentation – Official Microsoft documentation covering Virtual WAN architecture, configuration, and best practices
- Azure Virtual Network Manager Overview – Comprehensive guide to AVNM capabilities and implementation patterns
- Azure Architecture Centre: Hub-Spoke Topology – Microsoft’s reference architecture for traditional hub-spoke designs
- Gartner Magic Quadrant for WAN Edge Infrastructure – Industry analysis of SD-WAN and cloud networking trends
- Azure Pricing Calculator – Tool for estimating Azure networking costs across different architectures
- Azure Network Security Best Practices – Security guidance for Azure networking implementations
- ExpressRoute Documentation – Official guide to Azure ExpressRoute connectivity options and configuration
- Azure Cloud Adoption Framework: Network Decision Guide – Strategic guidance for Azure networking architecture decisions
- Forrester Total Economic Impact of Azure Networking – ROI analysis and business case research for Azure networking investments
- Azure Network Watcher – Monitoring and diagnostics tools for Azure networking troubleshooting and optimisation