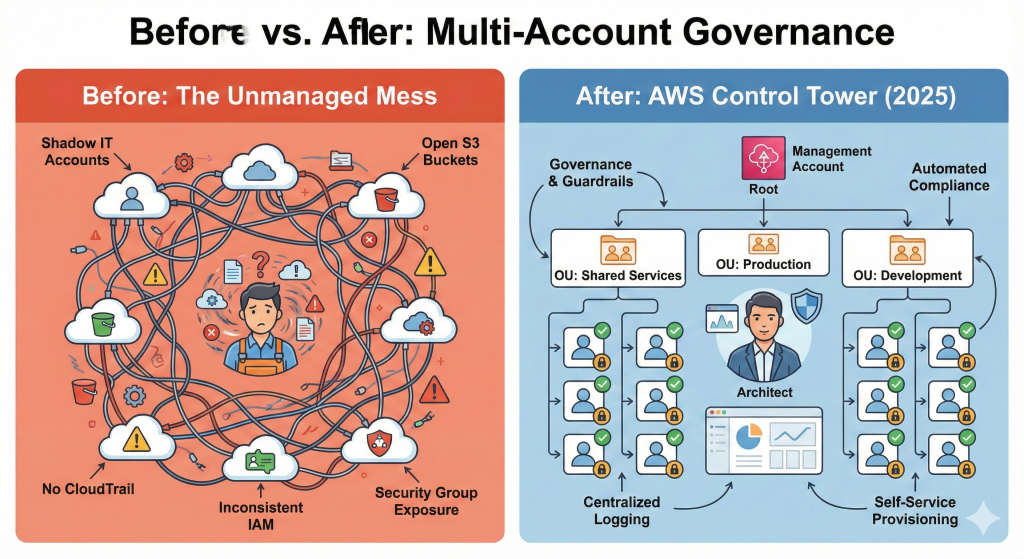
Here’s an uncomfortable truth: most organisations mess up AWS multi-account architecture from day one, then spend three years fixing it. I know this because I’ve lived both sides of it – as the junior engineer who created the mess by spinning up “just one more account” without thinking about governance, and later as the platform architect inheriting environments with tons of accounts, half of which no one could identify the owner for, security groups open to the world, and CloudTrail disabled in production “because it was expensive.”
I’ve watched platform teams struggle with hundreds of unmanaged accounts, security teams fighting configuration drift across environments they can’t even see, and compliance audits that reveal entire business units running in shadow IT accounts because the official provisioning process takes six weeks. The worst part? Everyone knows it’s broken, but fixing it whilst keeping the business running feels impossible.
AWS Control Tower exists to solve this exact problem, and the 2025 updates have finally made it flexible enough for real enterprises rather than just textbook examples. Games24x7, managing over 100 million users in India’s cutthroat online gaming sector, implemented Control Tower and recorded zero successful cybersecurity attacks whilst shipping new features weekly. That’s not luck or massive security spend – it’s what happens when your foundation architecture actually works.
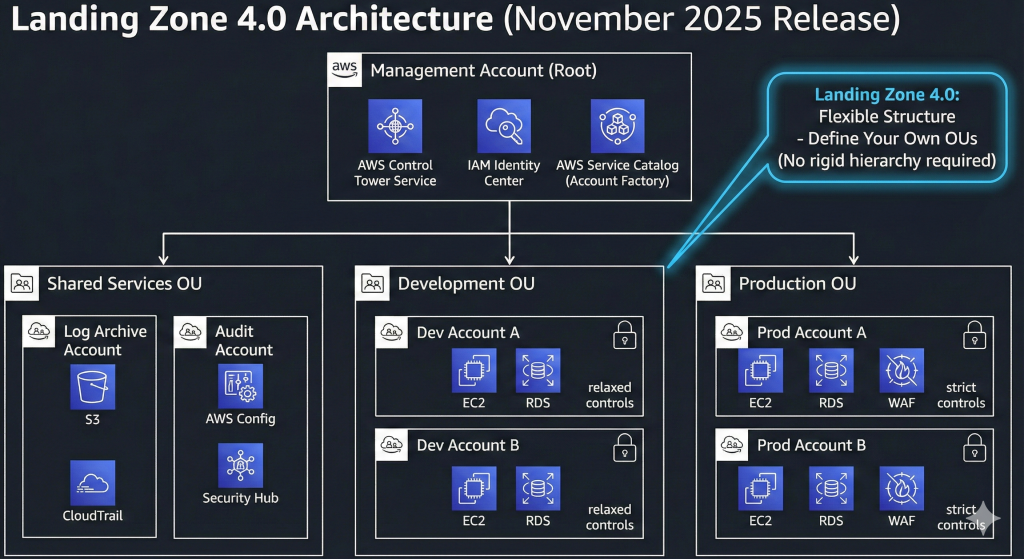
The traditional approach fails because organisations treat governance as something they’ll “add later” once they’ve got a few workloads running. By the time you hit 50 accounts, you’re drowning in inconsistent IAM policies, mysterious S3 buckets no one remembers creating, and security violations that take weeks to trace to responsible teams. Control Tower flips this model: governance first, then scale safely within those guardrails. Landing Zone 4.0, released November 2025, removes the rigid structure requirements that made earlier versions frustrating for organisations with established AWS patterns.
What Control Tower Actually Does (And Why It Matters)
Control Tower orchestrates multiple AWS services into a cohesive governance layer that sets up and manages a secure, compliant multi-account environment based on AWS best practices. Think of it as the missing operations layer between AWS Organizations (which just groups accounts) and your actual security and compliance requirements.
The platform deploys a landing zone – a pre-configured environment with organizational structure, shared accounts, and baseline controls – in under an hour. Your management account gets the Control Tower orchestration layer. Two mandatory shared accounts (Audit and Log Archive) receive security logs and AWS Config recordings from every enrolled account. Additional accounts deploy through Account Factory with pre-approved configurations that inherit governance policies automatically.
Before Control Tower, setting this up manually took platform teams 4-6 weeks of careful configuration. Miss a step and you’ve got accounts that bypass CloudTrail logging or lack proper isolation. Control Tower codifies AWS’s accumulated knowledge from thousands of enterprise deployments, so you’re not reinventing multi-account security from first principles.
The November 2025 Landing Zone 4.0 release addressed the biggest complaint: mandatory organizational structure. Previous versions forced everyone into the same rigid hierarchy regardless of actual business needs. Now you define your own OU structure whilst maintaining Control Tower governance. Optional service integrations let you disable AWS Config, Security Hub, CloudTrail, or AWS Backup if they conflict with existing tooling – crucial for enterprises migrating from competitor platforms.
The Controls That Actually Prevent Problems
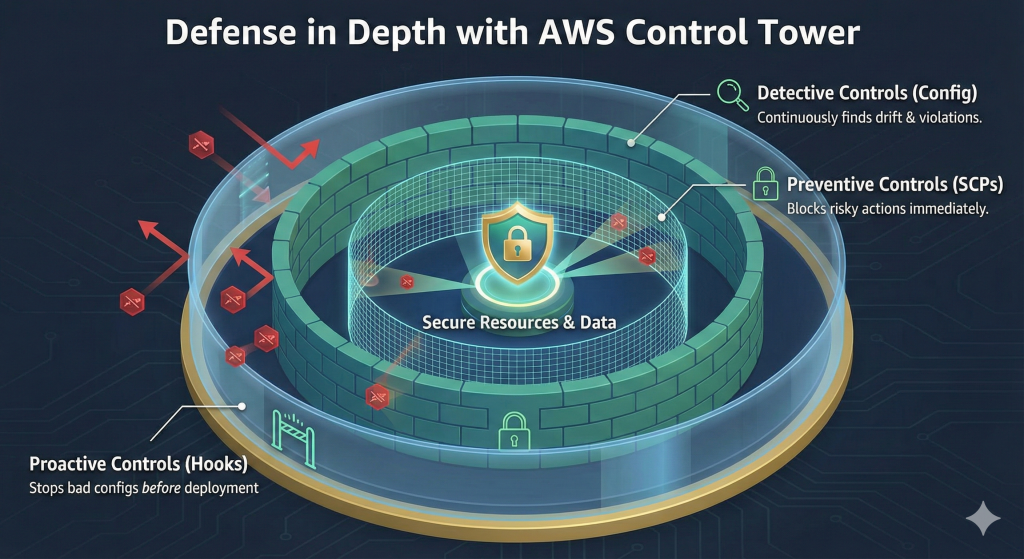
Control Tower provides over 750 managed controls deployable in minutes. These divide into three types that work together to create defence in depth:
Preventive controls use Service Control Policies to block risky actions before they happen. When a developer tries to disable CloudTrail logging or create an unencrypted S3 bucket in production, the action fails immediately. No security incident to investigate, no remediation work, no explaining to auditors why it happened. The most valuable preventive controls stop configuration changes that would weaken your security posture: disabling AWS Config recordings, modifying security group rules for management ports, or launching instances without approved AMIs.
Detective controls run AWS Config rules that continuously evaluate resource configurations and flag violations. Every 15 minutes, Config checks whether your resources match desired state. When someone creates an RDS instance without encryption, you get an alert within minutes rather than discovering it months later during an audit. Detective controls identify drift from baseline configurations, unusual IAM activity, and resources deployed without proper tagging.
Proactive controls use AWS CloudFormation hooks to evaluate resources during stack deployment, before they’re created. If a CloudFormation template tries to deploy non-compliant infrastructure, the stack fails before any resources provision. This shifts security left to the development phase where fixes cost pennies instead of pounds.
The November 2025 update added 279 AWS Config controls and enhanced relationship mapping. The Control Catalog now shows which controls complement each other (Config rule detecting violations + SCP preventing violations = comprehensive coverage), which conflict (mutually exclusive controls that can’t both be enabled), and which provide alternative approaches to the same risk. This intelligence helps you build coherent control sets rather than randomly enabling rules that cancel each other out.
Control Tower maps controls to industry frameworks including ACSC-Essential-Eight, ACSC-ISM, AWS-WAF, CCCS-Medium-Cloud-Control, CIS AWS Benchmark v1.2 and v1.3, and CIS v7.1. When auditors ask for evidence of CIS Benchmark compliance, you export the mapping showing which controls enforce each requirement.
Controls Dedicated Mode: For Organisations That Already Have Infrastructure
The Controls Dedicated experience launched November 2025 solves a major adoption barrier. Previously, using Control Tower meant deploying the full landing zone even if you already had a well-architected multi-account environment. Organisations with 200+ existing accounts weren’t going to tear everything down and rebuild just to access Control Tower’s controls.
Controls Dedicated mode provides access to the Control Catalog without requiring landing zone deployment. You maintain your existing account structure, organizational units, and operational processes whilst deploying specific controls to fill governance gaps. This incremental approach works for:
- Enterprises migrating from Azure or GCP who’ve built custom governance
- Organizations that implemented multi-account structure before Control Tower existed
- Companies with regulatory requirements that conflict with standard landing zone patterns
- Acquisitions where you’re inheriting existing AWS environments
You still get the control deployment automation, relationship mapping, and compliance framework alignment – just without the prescriptive landing zone structure. This makes Control Tower adoption a tactical decision rather than a strategic multi-year programme.
Account Factory: The Self-Service Portal That Actually Works
The promise of cloud has always been developer self-service provisioning. The reality in most enterprises is emailing the platform team, waiting two weeks for approval, then discovering the account has wrong networking configuration. Account Factory transforms this experience.
Account Factory provides configurable account templates through AWS Service Catalog. Your platform team defines account blueprints: development accounts with relaxed controls and internet access, production accounts with strict security policies and private networking, compliance accounts meeting regulatory requirements. Application teams request accounts through Service Catalog, select appropriate template, provide business justification, and receive fully configured accounts in under an hour.
The accounts inherit baseline configurations automatically: CloudTrail logging enabled and immutable, AWS Config recording all configuration changes, Security Hub aggregating findings, IAM Identity Center federation for user access, VPC networking connected to shared services, tagging standards enforced, budget alerts configured. No manual configuration, no drift, no accounts slipping through without proper governance.
Account Factory for Terraform extends this capability to infrastructure-as-code workflows. Platform teams define account vending logic in Terraform, storing configuration in version control and deploying through CI/CD pipelines. This supports custom provisioning patterns that standard Account Factory doesn’t address: specific cross-account IAM roles, third-party tool integration, custom resource tagging schemes, or specialized networking requirements.
The automatic enrollment feature released November 2025 eliminates a persistent pain point. Previously, when you moved an account between organizational units, you had to manually re-register it to apply the new OU’s controls. Now enrollment happens automatically – move an account from Development OU to Production OU and it immediately inherits production security policies whilst losing development-specific relaxed controls. This automation reduces drift and ensures accounts maintain appropriate governance as projects mature from development to production.
Real Enterprise Implementations
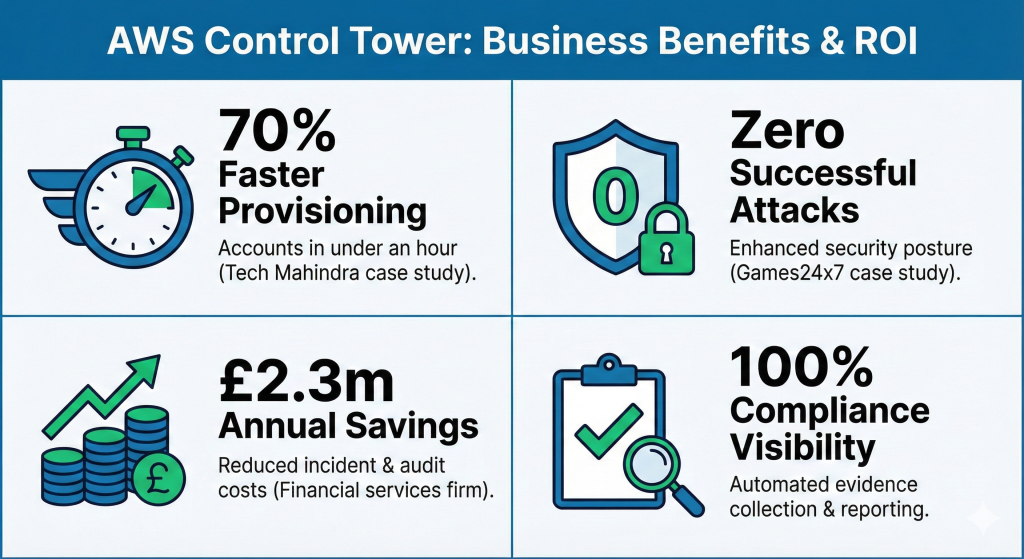
Tech Mahindra operates multi-customer cloud deployments across regulated industries where data residency requirements often blocked cloud adoption. Customer contracts mandate in-country data storage, creating legal and regulatory barriers. Control Tower’s data residency features and Account Factory automation reduced their account provisioning time by 70%, letting them address customer compliance requirements whilst maintaining consistent security policies across global operations. When a new customer requires India-region deployment with specific compliance controls, Tech Mahindra provisions the complete environment in under an hour instead of the previous multi-week process.
Games24x7 manages over 100 million users across India’s online gaming platforms (RummyCircle and My11Circle). The gaming industry experienced a 167% increase in API attacks between 2021 and 2022, making it one of the most targeted sectors. Control Tower provided the multi-account governance foundation whilst AWS Config handled configuration management, Amazon GuardDuty detected threats, and IAM Identity Center managed identity. Since implementation, Games24x7 has recorded zero successful cybersecurity attacks. Their attack surface score improved by 25%, and they established centralized access management whilst maintaining full compliance with Indian data protection laws. This isn’t about massive security budgets – it’s architecture that makes attacks expensive for adversaries.
A UK financial services firm with over 200 AWS accounts estimated £2.3 million in annual savings from Control Tower implementation. The breakdown: £900,000 from reduced security incident costs (preventive controls stopping problems before they become incidents), £400,000 from compliance audit efficiency (automated evidence collection instead of manual documentation), £600,000 from eliminated manual governance labour (no more weekly account audits and manual policy enforcement), and £400,000 from faster time-to-market for new services (account provisioning dropping from weeks to hours). The 12-month payback period made this an easy CFO conversation.
Getting Started Without Breaking Everything
Most organisations implementing Control Tower make one of three mistakes: over-engineering before understanding requirements, treating it as a one-time project instead of ongoing operations, or ignoring the organizational change management required for self-service adoption.
Start Small and Learn
Deploy Control Tower in a sandbox environment first. Create the landing zone, provision test accounts through Account Factory, enable some controls, intentionally violate them to understand how detection works. Break things in ways that won’t affect production. This learning phase takes 2-4 weeks but prevents painful mistakes during actual rollout.
Don’t design the perfect organizational structure upfront. You lack the context to make good decisions about which accounts belong in which OUs until you’ve operated the environment. Start with simple structure (Sandbox, Development, Production) and refine based on actual governance requirements that emerge. Landing Zone 4.0’s flexibility means early structure decisions aren’t permanent.
Phased Rollout
Month 1-2: Deploy landing zone, configure organizational units, enable mandatory controls, provision first development accounts through Account Factory. Get platform team comfortable with Control Tower operations.
Month 3-4: Migrate pilot workload from existing account to Control Tower-managed account. Validate that governance controls don’t break applications. Document friction points and adjust policies. Train application team on self-service provisioning.
Month 5-12: Scale to additional workloads. Refine Account Factory templates based on actual requirements. Add elective controls addressing security gaps discovered during operation. Enroll existing accounts if beneficial.
This gradual approach lets you validate assumptions before committing hundreds of accounts. Each phase builds confidence that governance enables rather than blocks.
Common Implementation Pitfalls
Don’t enable every available control just because you can. Start with AWS-recommended mandatory controls plus selective elective controls addressing your specific risks. You can always add more controls later; removing controls after they’ve broken workflows is politically harder.
Don’t create organizational unit hierarchies mirroring your company org chart. Cloud organizational structure should reflect technical governance requirements, not business reporting structures. Group accounts by risk profile and compliance requirements: strict production controls, relaxed development policies, specialized compliance environments.
Don’t skip the change management work. Control Tower succeeds technically but fails organizationally when application teams bypass self-service provisioning because they don’t understand it or don’t trust it. Clear documentation, hands-on training, and visible executive support matter more than technical perfection.
Integration with Existing Security Tooling
Control Tower doesn’t replace your security stack – it provides the governance foundation that makes your security tools more effective. Security Hub aggregates findings from GuardDuty, Inspector, Macie, IAM Access Analyzer, and third-party security tools into a centralized dashboard across all accounts. Controls enforce that Security Hub stays enabled and findings can’t be suppressed without justification.
Config continuously records resource configurations and evaluates them against your compliance rules. Control Tower ensures Config runs in every account with recordings stored in immutable Log Archive account. When auditors ask “prove that encryption was enabled on all databases during Q3 2024,” Config provides the evidence without manual investigation.
CloudTrail logs all API activity across your organization. Control Tower enforces that CloudTrail remains enabled with logs stored in accounts that application teams can’t access or modify. This creates an immutable audit trail crucial for security investigations and compliance reporting.
IAM Identity Center provides federated access to accounts through your corporate identity provider. Instead of managing individual IAM users across hundreds of accounts, users authenticate once and receive temporary credentials for accounts they’re authorized to access. Control Tower configures Identity Center during landing zone deployment and enforces that it remains the primary access path.
Cost Realities and Ongoing Operations
Control Tower itself carries no licensing fees. You pay only for underlying services: AWS Config rules recording configuration changes (£0.003 per configuration item recorded), CloudTrail logs stored in S3 (standard S3 pricing), Security Hub findings aggregated (£0.0010 per check per account per month). For a 100-account environment, expect £15,000-£40,000 monthly for these services depending on activity levels and retention requirements.
Implementation typically requires 3-6 months of platform team effort. Budget £150,000-£250,000 in labour costs: 1-2 cloud architects designing organizational structure and control sets, 1-2 platform engineers implementing landing zone and Account Factory templates, part-time security engineer validating controls, part-time compliance specialist mapping to regulatory requirements.
Ongoing operations need 0.5-1 FTE platform engineer (£50,000-£100,000 annually) monitoring Control Tower health, investigating drift, refining policies based on violation patterns, and extending governance to new regions or business units. This seems expensive until you compare it to pre-Control Tower operations: manual account provisioning, weekly configuration audits, firefighting security violations, and explaining compliance failures to auditors.
The ROI comes from automation and prevention. Account provisioning drops from 2-4 weeks to under an hour (70% time reduction). Security violations decrease by 40% because preventive controls stop problems before they occur. Compliance audit preparation shrinks from weeks to days because evidence collection is automated. Platform team capacity shifts from reactive firefighting to strategic initiatives.
What Control Tower Won’t Solve
Control Tower provides multi-account governance, not application-level security. It won’t secure your applications, design your VPC architecture, or implement zero trust networking. You still need application security controls, runtime protection, secrets management, and all the other security layers.
Control Tower works brilliantly for AWS-centric organizations. If you’re truly multi-cloud with significant Azure or GCP deployments, Control Tower’s AWS-specific governance creates operational overhead. You’ll need separate governance implementations for each cloud plus coordination to maintain consistent policies across platforms.
Control Tower assumes you want prescriptive best practices. Organizations with unusual requirements or sophisticated custom governance may find Control Tower’s opinions limiting despite Landing Zone 4.0’s increased flexibility. Sometimes you actually do need the complexity that Control Tower tries to abstract away.
Looking Ahead: Where Control Tower Goes Next
Machine learning will increasingly suggest policy optimizations based on violation patterns. When the same control generates hundreds of false positives because it doesn’t understand your legitimate use case, Control Tower should notice and suggest refinement. AWS already has the data from Security Hub and Config – applying ML to identify policy improvement opportunities is the logical next step.
Multi-cloud governance remains a pain point as 92% of enterprises adopt multi-cloud strategies. AWS has no incentive to help you govern Azure or GCP, but partner ecosystems will fill this gap. Expect tools that compile policies into Control Tower controls, Azure Policy definitions, and GCP organization policies from a single source of truth.
Zero trust architecture integration will deepen. Control Tower currently focuses on account-level governance, but the industry moves toward continuous verification and context-aware access. Future versions should enforce zero trust principles by default: every access request evaluated against device posture, user behaviour patterns, and risk scores before granting temporary credentials.
Making the Decision
Control Tower makes sense for AWS-centric organizations needing rapid multi-account environment deployment with automated compliance. If you’re starting fresh on AWS or your current environment has under 50 accounts, Control Tower accelerates time-to-value whilst embedding security best practices from day one.
Organizations with 100+ existing accounts should evaluate Controls Dedicated mode for incremental adoption. You keep your current structure whilst filling specific governance gaps. This tactical approach avoids the disruption of wholesale migration whilst still accessing Control Tower’s control library and compliance mappings.
Multi-cloud organizations with significant non-AWS workloads need to think harder about the cost-benefit trade-off. Control Tower governance won’t extend to Azure or GCP, creating operational overhead managing multiple governance implementations. You might be better served by multi-cloud governance platforms that abstract across providers.
The foundation architecture you build determines whether your platform team enables or blocks innovation. Control Tower shifts the burden from your team designing and maintaining custom governance to operating and refining AWS-provided patterns. For most organizations, that’s the right trade-off.
Useful Links
AWS Official Documentation:
- AWS Control Tower User Guide: https://docs.aws.amazon.com/controltower/latest/userguide/
- AWS Control Tower Features: https://aws.amazon.com/controltower/features/
- AWS Control Tower FAQs: https://aws.amazon.com/controltower/faqs/
Recent Updates and Announcements:
- Landing Zone 4.0 Release Notes: https://docs.aws.amazon.com/controltower/latest/userguide/2025-all.html
- Controls Dedicated Experience: https://aws.amazon.com/blogs/aws/aws-control-tower-introduces-a-controls-dedicated-experience/
- Automatic Account Enrolment: https://aws.amazon.com/about-aws/whats-new/2025/11/aws-control-tower-automatic-enrollment/
Case Studies:
- Games24x7 Implementation: https://aws.amazon.com/solutions/case-studies/games24x7-case-study-2024/
- AWS Control Tower Customer Stories: https://aws.amazon.com/controltower/customers/
Implementation Guidance:
- AWS Multi-Account Strategy Best Practices: https://aws.amazon.com/organizations/getting-started/best-practices/
- Account Factory for Terraform: https://docs.aws.amazon.com/controltower/latest/userguide/aft-overview.html
- Control Catalog Overview: https://docs.aws.amazon.com/controltower/latest/controlreference/control-catalog.html